IT Fundamentals/Collection
IT Fundamentals
[edit | edit source]IT Fundamentals introduces computer hardware, computer software, databases, networking, security, and software development.
This course comprises 15 lessons covering IT fundamentals. Each lesson includes a combination of Wikipedia readings, YouTube videos, and hands-on learning activities. The course also assists learners in preparing for CompTIA IT Fundamentals certification.
This entire Wikiversity course can be downloaded in book form by selecting Download Learning Guide in the sidebar.
Preparation
[edit | edit source]This is a college-level introductory computer support course. Learners should already be familiar with introductory computer concepts.
Lessons
[edit | edit source]Current Lessons
[edit | edit source]Current lessons targeting IT Fundamentals exam FC0-U61:
- Introduction
- Devices
- Components
- Peripherals
- Operating Systems
- Applications
- Database Concepts
- Database Use
- Networking
- Internet
- Security Concepts
- Security Practices
- Software Development
- Troubleshooting
- Business Continuity
See Also
[edit | edit source]Bibliography
[edit | edit source]- Carswell, R., et al. (2012). Guide to Parallel Operating Systems with Windows 7 and Linux, 2nd Edition. Cengage. ISBN 9781111543709
- CompTIA. (2014). CompTIA: IT Fundamentals Exam Objectives FC0-U51
- CompTIA. (2018). CompTIA: IT Fundamentals (ITF+) Exam Objectives FC0-U61
- Docter, Q. (2015). CompTIA IT Fundamentals Study Guide: Exam FC0-U51. Sybex. ISBN 9781119096481
- Docter, Q. (2018). CompTIA IT Fundamentals (ITF+) Study Guide: Exam FC0-U61 2nd Edition. Wiley. ISBN 9781119513124
- Smith, A. and Wempen, F. (2011). CompTIA Strata Study Guide. Wiley. ISBN 9780470977422
Introduction
[edit | edit source]
This lesson introduces IT Fundamentals. Topics include course overview, data, and information concepts.
Objectives and Skills
[edit | edit source]Objectives and skills for the introduction portion of IT Fundamentals certification include:[1]
- Overview.
- IT concepts and terminology
- Infrastructure
- Applications and software
- Software development
- Database fundamentals
- Security
- Compare and contrast notational systems.
- Binary
- Hexadecimal
- Decimal
- Data representation
- ASCII
- Unicode
- Illustrate the basics of computing and processing.
- Input
- Processing
- Output
- Storage
- Explain the value of data and information.
- Data and information as assets
- Importance of investing in security
- Relationship of data to creating information
- Intellectual property
- Trademarks
- Copyright
- Patents
- Digital products
- Data-driven business decisions
- Data capture and collection
- Data correlation
- Meaningful reporting
Readings
[edit | edit source]- Wikipedia: CompTIA
- Wikipedia: Numeral system
- Wikipedia: Character encoding
- Wikipedia: Information technology
- Wikipedia: Intellectual property
Multimedia
[edit | edit source]- YouTube: CompTIA IT Fundamentals+ (FC0-U61) Exam Prep Overview
- YouTube: Notational Systems
- YouTube: Value of Data & Information
- YouTube: Intellectual Property
- YouTube: Chapter 1 - IT Fundamentals+ (FC0-U61) How People Use Computers
Activities
[edit | edit source]- Consider the impact of information technology in your current student or work environment.
- What information systems do you use? What data is processed? What information is provided?
- What infrastructure (devices and networks) do you use?
- What applications and software do you use? Which operating systems are you familiar with (PC, mobile)?
- What programming experience do you have?
- What databases have you used?
- How do you apply computer security best practices? Do you have backups for disaster recovery?
- Complete the tutorial Owlcation: How to Convert Hex to Binary and Binary to Hexadecimal. Practice converting values between decimal, binary, and hexadecimal.
- Windows: Review Adelphi: Windows Calculator. Use the Windows Calculator to convert between decimal, binary, and hexadecimal.
- macOS: Review OSX Daily: Access the Scientific Calculator & Programmer Calculator in Mac OS X. Use the macOS Calculator to convert between decimal, binary, and hexadecimal.
- Linux: Review Linux Journal: Fancy Tricks for Changing Numeric Base. Use bc to convert between decimal, binary, and hexadecimal.
- Mobile: Download a free programmer or developer calculator from the app store and use it to convert between decimal, binary, and hexadecimal.
- Review Wikipedia: ASCII.
- Windows: Review Wikipedia: Alt code. On a PC with a numeric keypad, open Notepad and then use Alt codes to enter the ASCII value for the characters in your first name. Observe how the ASCII values are converted into standard display characters just as if you had typed those characters on the keyboard.
- Other: Use Rapid Tables: ASCII Text to Hex Code Converter. Convert your name from ASCII to hex values.
- Review Wikipedia: Unicode input. Insert special characters into a text document:
- Windows: Run the Notepad application and use the Character Map utility to select special characters and paste them into Notepad.
- macOS: Run the TextEdit application and insert special characters into the text file.
- Linux: Run the gedit application and use the GNOME Character Map utility to select special characters and paste them into gedit.
- Review World Intellectual Property Organization: What is Intellectual Property?. Consider the impact of intellectual property rights in your current student or work environment. What trademarks and patents are you familiar with? What copyrighted resources do you regularly access? Do you access these resources legally?
- Review Wikipedia: Data-informed decision-making. Consider the impact of data collection, data analysis, and data reporting in your current student or work environment. Would you describe the impact as "data based decision making" or "data-informed decision making"? What is the difference between these two approaches from your perspective?
Lesson Summary
[edit | edit source]Overview
[edit | edit source]
- CompTIA IT Fundamentals certification covers IT concepts and terminology, infrastructure, applications and software, software development, database fundamentals, and security.[2]
- IT concepts and terminology include data representation, data processing, and information value.[3]
- Infrastructure includes devices, components, networking, and Internet services.[4]
- Applications and software include operating systems, applications, and uses.[5]
- Software development includes programming languages and program structure.[6]
- Database fundamentals include database concepts and use.[7]
- Security includes security concepts and best practices, as well as business continuity through fault tolerance and disaster recovery.[8]
Notation systems
[edit | edit source]
- A numeral system is a writing system for expressing numbers; that is, a mathematical notation for representing numbers of a given set, using digits or other symbols in a consistent manner.[9]
- A binary number is a number expressed in the base-2 numeral system or binary numeral system, which uses only two symbols: typically "0" (zero) and "1" (one).[10]
- The decimal numeral system (also called base-ten positional numeral system) is the standard system for denoting integer and non-integer numbers using the symbols "0"–"9".[11]
- Hexadecimal (also base 16, or hex) is a positional system that represents numbers using a base of 16. Unlike the common way of representing numbers with ten symbols, it uses sixteen distinct symbols, most often the symbols "0"–"9" to represent values zero to nine, and "A"–"F" (or alternatively "a"–"f") to represent values ten to fifteen.[12]
Data representation
[edit | edit source]
- Character encoding is used to represent a repertoire of characters by some kind of encoding system. Depending on the abstraction level and context, corresponding code points and the resulting code space may be regarded as bit patterns, octets, natural numbers, electrical pulses, etc.[13]
- ASCII (American Standard Code for Information Interchange) is a character encoding standard for electronic communication used to represent text in computers, telecommunications equipment, and other devices.[14]
- Unicode is an information technology standard for the consistent encoding, representation, and handling of text expressed in most of the world's writing systems.[15]
- Unicode can be implemented by different character encodings. The Unicode standard defines UTF-8, UTF-16, and UTF-32.[16]
- UTF-8 is the dominant encoding used on the World Wide Web and uses one byte for the first 128 code points, and up to 4 bytes for other characters.[17]
- The first 128 Unicode code points represent the ASCII characters, which means that any ASCII text is also a UTF-8 text.[18]
Information Systems
[edit | edit source]
- Information technology (IT) is the use of computers to store, retrieve, transmit, and manipulate data or information.[19]
- A data processing system is a combination of machines, people, and processes that for a set of inputs produces a defined set of outputs. The inputs and outputs are interpreted as data, facts, information etc. depending on the interpreter's relation to the system.[20]
- Input/output or I/O (or, informally, IO) is the communication between an information processing system, such as a computer, and the outside world, possibly a human or another information processing system.[21]
- Inputs are the signals or data received by the system and outputs are the signals or data sent from it.[22]
- Processing includes any computations performed by an information system on the inputs in order to generate the associated outputs.[23]
- Computer data storage is a technology consisting of computer components and recording media that are used to retain digital data.[24]
- In practice, almost all computers use a storage hierarchy which puts fast but expensive and small storage options close to the central processing unit (CPU) and slower but less expensive and larger options further away.[25]
- Generally the fast volatile storage technologies (which lose data when power is off) are referred to as "memory", while slower persistent technologies are referred to as "storage".[26]
- A peripheral or peripheral device is an ancillary device used to put information into and get information out of the computer.[27]
Data and information
[edit | edit source]


- Data is any sequence of one or more symbols given meaning by specific act(s) of interpretation. Data requires interpretation to become information.[28]
- Information is associated with data, as data represents values attributed to parameters, and information is data in context and with meaning attached.[29]
- A digital asset is anything that exists in a binary format and comes with the right to use.[30]
- Information security, sometimes shortened to infosec, is the practice of protecting information by mitigating information risks.[31]
- Intellectual property (IP) is a category of property that includes intangible creations of the human intellect. There are many types of intellectual property, including copyrights, patents, trademarks, and trade secrets.[32]
- A trademark is a type of intellectual property consisting of a recognizable sign, design, or expression which identifies products or services of a particular source from those of others.[33]
- Copyright is the exclusive right given to the creator of a creative work to reproduce the work, usually for a limited time.[34]
- A patent is a form of intellectual property that gives its owner the legal right to exclude others from making, using, selling and importing an invention for a limited period of years, in exchange for publishing an enabling public disclosure of the invention.[35]
- Digital products are those represented and stored using the binary number system of ones (1) and zeros (0).[36]
- Data-informed decision-making (DIDM) gives reference to the collection and analysis of data to guide decisions that improve success.[37] Data-informed decision-making is based on a sequence of data collection, data analysis, and data reporting.
- Data collection is the process of gathering and measuring information on targeted variables in an established system, which then enables one to answer relevant questions and evaluate outcomes.[38]
- Data analysis is a process of inspecting, cleansing, transforming and modeling data with the goal of discovering useful information, informing conclusion and supporting decision-making.[39]
- Data reporting is the process of collecting and submitting data which gives rise to accurate analyses of the situation.[40]
Key Terms
[edit | edit source]
- ASCII (American Standard Code for Information Interchange)
- A character encoding standard for electronic communication used to represent text in computers, telecommunications equipment, and other devices.[41]
- DRM (Digital Rights Management)
- A set of access control technologies for restricting the use of proprietary hardware and copyrighted works.[42]
- Unicode
- An information technology standard for the consistent encoding, representation, and handling of text expressed in most of the world's writing systems.[43]
- UTF (Unicode Transformation Format)
- A Unicode encoding that maps code points to byte sequences. Encodings include UTF-8, UTF-16, and UTF-32.[44]
Assessments
[edit | edit source]See Also
[edit | edit source]- IC3
- IONOS: ASCII - American Standard Code for Information Interchange]
- Smashing Magazine: Unicode, UTF8 & Character Sets: The Ultimate Guide
- NOLO: Which Protection Do I Need: Patent, Copyright, or Trademark?
References
[edit | edit source]- ↑ CompTIA: IT Fundamentals (ITF+) Exam Objectives FC0-U61
- ↑ CompTIA: IT Fundamentals (ITF+) Exam Objectives FC0-U61
- ↑ CompTIA: IT Fundamentals (ITF+) Exam Objectives FC0-U61
- ↑ CompTIA: IT Fundamentals (ITF+) Exam Objectives FC0-U61
- ↑ CompTIA: IT Fundamentals (ITF+) Exam Objectives FC0-U61
- ↑ CompTIA: IT Fundamentals (ITF+) Exam Objectives FC0-U61
- ↑ CompTIA: IT Fundamentals (ITF+) Exam Objectives FC0-U61
- ↑ CompTIA: IT Fundamentals (ITF+) Exam Objectives FC0-U61
- ↑ Wikipedia: Numeral system
- ↑ Wikipedia: Binary number
- ↑ Wikipedia: Decimal
- ↑ Wikipedia: Hexadecimal
- ↑ Wikipedia: Character encoding
- ↑ Wikipedia: ASCII
- ↑ Wikipedia: Unicode
- ↑ Wikipedia: Unicode
- ↑ Wikipedia: Unicode
- ↑ Wikipedia: Unicode
- ↑ Wikipedia: Information technology
- ↑ Wikipedia: Data processing system
- ↑ Wikipedia: Input/output
- ↑ Wikipedia: Input/output
- ↑ Wikipedia: IPO model
- ↑ Wikipedia: Computer data storage
- ↑ Wikipedia: Computer data storage
- ↑ Wikipedia: Computer data storage
- ↑ Wikipedia: Peripheral
- ↑ Wikipedia: Data (computing)
- ↑ Wikipedia: Information
- ↑ Wikipedia: Digital asset
- ↑ Wikipedia: Information security
- ↑ Wikipedia: Intellectual property
- ↑ Wikipedia: Trademark
- ↑ Wikipedia: Copyright
- ↑ Wikipedia: Patent
- ↑ Wikipedia: Digital data
- ↑ Wikipedia: Data-informed decision-making
- ↑ Wikipedia: Data collection
- ↑ Wikipedia: Data analysis
- ↑ Wikipedia: Data reporting
- ↑ Wikipedia: ASCII
- ↑ Wikipedia: Digital rights management
- ↑ Wikipedia: Unicode
- ↑ Wikipedia: Unicode
Devices
[edit | edit source]
This lesson introduces computing devices and common units of measure for data.
Objectives and Skills
[edit | edit source]Objectives and skills for the devices portion of IT Fundamentals certification include:[1]
- Compare and contrast common computing devices and their purposes.
- Mobile phones
- Tablets
- Laptops
- Workstations
- Servers
- Gaming consoles
- IoT
- Home appliances
- Home automation devices
- Thermostats
- Security systems
- Modern cars
- IP cameras
- Streaming media devices
- Medical devices
- Compare and contrast common units of measure.
- Storage unit
- Bit
- Byte
- KB
- MB
- GB
- TB
- PB
- Throughput unit
- bps
- Kbps
- Mbps
- Gbps
- Tbps
- Processing speed
- MHz
- GHz
- Storage unit
Readings
[edit | edit source]- Wikipedia: Computer
- Wikipedia: Mobile device
- Wikipedia: Internet of things
- Wikipedia: Units of information
Multimedia
[edit | edit source]- YouTube: Common Computing Devices & Their Purposes
- YouTube: Units of Measure
- YouTube: Chapter 4 - IT Fundamentals+ (FC0-U61) Data Storage and Sharing
Activities
[edit | edit source]- Together with classmates or friends, gather as many different types of computing devices as you have access to. If you are working alone, consider visiting your favorite electronics store to "comparison shop", but don't buy anything! Compare and contrast different computing devices. What do you like and dislike about each one? Is your opinion based on physical characteristics of the device (size, shape, appearance, etc.), performance characteristics, ergonomics (usability, operating system, software design, etc.), or vendor reputation?
- Compare and contrast workstations, servers, and gaming computers. Which companies are the top three vendors in each category? What is the price range for a typical device in each category and what usage differentiates when someone would purchase each one? How are storage and processing speed measured for these devices (KB, MB, GB, TB, PB, MHz, GHz)?
- Compare and contrast mobile phones, tablets, and laptops. Which companies are the top three vendors in each category? What is the price range for a typical device in each category and what usage differentiates when someone would purchase each one? How are storage and processing speed measured for these devices (KB, MB, GB, TB, PB, MHz, GHz)?
- Review How-To Geek: How to Pair a Bluetooth Device to Your Computer, Tablet, or Phone. Practice pairing a Bluetooth device to your computer or mobile device.
- Review CNet: Everything you need to know about NFC and mobile payments. Consider configuring your mobile device for NFC payments.
- Consider the impact of Internet-of-Things (IoT) on your daily life. What Internet-enabled devices are currently in use in your home, school, and/or work environments? What benefits do these devices provide? What risks come with using these devices? Include devices such as home appliances, home automation, thermostats, security systems, cars, IP cameras, streaming media, and medical devices.
Lesson Summary
[edit | edit source]






Common Computing Devices
[edit | edit source]Common computing devices include mobile phones, tablets, laptops, workstations, servers, and gaming consoles.
- A mobile phone is a portable telephone that can make and receive calls over a radio frequency link while the user is moving within a telephone service area. Modern mobile telephone services use a cellular network architecture. In addition to telephony, current mobile phones support a variety of other services, such as text messaging, MMS, email, Internet access, short-range wireless communications (infrared, Bluetooth), business applications, video games, and digital photography.[2]
- A tablet computer, commonly shortened to tablet, is a mobile device with a mobile operating system and touchscreen display and a rechargeable battery in a single, thin and flat package. Tablets, being computers, do what other personal computers do, but lack some input/output (I/O) abilities that others have. Modern tablets largely resemble modern smartphones, the only differences being that tablets are relatively larger than smartphones, with screens 7 inches (18 cm) or larger, measured diagonally, and may not support access to a cellular network.[3]
- A laptop is a small, portable personal computer (PC) with a "clamshell" form factor, typically having a thin LCD or LED computer screen mounted on the inside of the upper lid of the clamshell and an alphanumeric keyboard on the inside of the lower lid.[4]
- A workstation is a stationary personal computer, typically with a separate case holding the system components. Workstations have an external monitor with a display screen and an external keyboard, which are plugged into USB ports on the back of the computer case. Traditionally, the term workstation referred to systems used in high-end technical applications, and desktop computer referred to systems used in more common applications.[5]
- An all-in-one desktop computer or workstation integrates the system's internal components into the same case as the display, thus occupying a smaller footprint (with fewer cables) than desktops that incorporate a tower.[6]
- A server is a computer that provides functionality for other programs or devices, called "clients". This architecture is called the client–server model, and a single overall computation is distributed across multiple processes or devices. Servers can provide various functionalities, often called "services", such as sharing data or resources among multiple clients, or performing computation for a client. Typical servers are database servers, file servers, mail servers, print servers, web servers, game servers, and application servers. Hardware requirement for servers vary widely, depending on the server's purpose and its software. Servers are typically more powerful and expensive than the clients that connect to them.[7]
- A video game console is a computer device that outputs a video signal or visual image to display a video game that one or more people can play.[8]
Internet of Things (IoT)
[edit | edit source]
The Internet of things (IoT) is a system of interrelated computing devices, mechanical and digital machines provided with unique identifiers (UIDs) and the ability to transfer data over a network without requiring human-to-human or human-to-computer interaction.[9] Common IoT devices include:
- Home appliances
- Home automation devices
- Thermostats
- Security systems
- Modern cars
- IP cameras
- Streaming media devices
- Medical devices
Common Units of Measure
[edit | edit source]
- A bit is the smallest unit of information. The name bit is a portmanteau of binary digit. Bits have only one of two possible values, most commonly represented as either 0 or 1.[10]
- A byte is a unit of digital information that most commonly consists of eight bits. There are 256 possible values for a byte (28), and the range of values for an unsigned byte is 0 - 255.[11]
- Units of information are typically measured in multiples of either bits or bytes. Bits are abbreviated with a lower-case b. Bytes are abbreviated with an upper-case B.[12]
- Traditionally, bits and bytes were measured in multiples of 2, so a kilobit was 1,024 bits (210). A lower-case prefix is used to indicate multiples of 10. An upper-case prefix is used to indicate multiples of 2.[13]
Storage Prefix Common Bits Bytes Base 10 Base 2 kilo thousand kb, Kb kB, KB 103 210 (1024) mega million mb, Mb mB, MB 106 220 (10242) giga billion gb, Gb gB, GB 109 230 (10243) tera trillion tb, Tb tB, TB 1012 240 (10244) peta thousand trillion pb, Pb pB, PB 1015 250 (10245)
- Data transfer rates, sometimes referred to as throughput, are typically measured in multiples of bits per second (bps), such as:[14]
Data Transfer (Throughput) Prefix Common Bits Base 10 Base 2 kilo thousand kbps, Kbps 103 210 (1024) mega million mbps, Mbps 106 220 (10242) giga billion gbps, Gbps 109 230 (10243) tera trillion tbps, Tbps 1012 240 (10244)
- Processing speed is measured in Hertz, or cycles per second.[15]
Processing Speed Prefix Common Hertz mega million MHz giga billion GHz
Key Terms
[edit | edit source]- AC (Alternating Current)
- An electric current which periodically reverses direction, and the form of electrical energy that consumers typically use when they plug devices into a wall socket.[16]
- airplane mode
- A setting available on smartphones and other portable devices that, when activated, suspends the device's radio-frequency (RF) signal transmission technologies (i.e., Bluetooth, telephony and Wi-Fi), effectively disabling all voice, text and phone services.
- AIO (All In One)
- A desktop computer that integrates the system's internal components into the same case as the display, thus occupying a smaller footprint (with fewer cables) than desktops that incorporate a tower.[17]
- DC (Direct Current)
- The unidirectional flow of an electric charge, and the form of electrical energy that consumers typically use when they run devices from a battery.[18]
- Gb (Gigabit)
- A unit of digital storage in bits equivalent to 109 (1 billion) for gb or 230 (1,0243) for Gb.[19]
- GB (Gigabyte)
- A unit of digital storage in bytes equivalent to 109 (1 billion) for gB or 230 (1,0243) for GB.[20]
- Gbps (Gigabit per second)
- A unit of data transfer in bits per second equivalent to 109 (1 billion) for gbps or 230 (1,0243) for Gbps.[21]
- GHz (Gigahertz)
- A unit of processing speed equivalent to 109 (1 billion) cycles per second.[22]
- IoT (Internet of Things)
- A system of interrelated computing devices, mechanical and digital machines provided with unique identifiers (UIDs) and the ability to transfer data over a network without requiring human-to-human or human-to-computer interaction.[23]
- Kb (Kilobit)
- A unit of digital storage in bits equivalent to 103 (1 thousand) for kb or 210 (1,024) for Kb.[24]
- KB (Kilobyte or Knowledge Base)
- A unit of digital storage in bytes equivalent to 103 (1 thousand) for kB or 210 (1,024) for KB.[25]
- Kbps (Kilobit per second)
- A unit of data transfer in bits per second equivalent to 103 (1 thousand) for kbps or 210 (1,024) for Kbps.[26]
- Mb (Megabit)
- A unit of digital storage in bits equivalent to 106 (1 million) for mb or 220 (1,0242) for Mb.[27]
- MB (Megabyte)
- A unit of digital storage in bytes equivalent to 106 (1 million) for mB or 220 (1,0242) for MB.[28]
- Mbps (Megabit per second)
- A unit of data transfer in bits per second equivalent to 106 (1 million) for mbps or 220 (1,0242) for Mbps.[29]
- MHz (Megahertz)
- A unit of processing speed equivalent to 106 (1 million) cycles per second.[30]
- PB (Petabyte)
- A unit of digital storage in bytes equivalent to 1015 (1,000 trillion) for pB or 250 (1,0245) for PB.[31]
- PC (Personal Computer)
- A multi-purpose computer whose size, capabilities, and price make it feasible for individual use.[32]
- Tb (Terabit)
- A unit of digital storage in bits equivalent to 1012 (1 trillion) for tb or 240 (1,0244) for Tb.[33]
- TB (Terabyte)
- A unit of digital storage in bytes equivalent to 1012 (1 trillion) for tB or 240 (1,0244) for TB.[34]
- Tbps (Terabits per second)
- A unit of data transfer in bits per second equivalent to 1012 (1 trillion) for tbps or 240 (1,0244) for Tbps.[35]
Assessments
[edit | edit source]- Flashcards: Quizlet: IT Fundamentals - Devices
- Quiz: Quizlet: IT Fundamentals - Devices
See Also
[edit | edit source]References
[edit | edit source]- ↑ CompTIA: IT Fundamentals (ITF+) Exam Objectives FC0-U61
- ↑ Wikipedia: Mobile phone
- ↑ Wikipedia: Tablet computer
- ↑ Wikipedia: Laptop
- ↑ Wikipedia: Personal computer
- ↑ Wikipedia: Desktop computer
- ↑ Wikipedia: Server (computing)
- ↑ Wikipedia: Video game console
- ↑ Wikipedia: Internet of things
- ↑ Wikipedia: Bit
- ↑ Wikipedia: Byte
- ↑ Wikipedia: Data-rate units
- ↑ Wikipedia: Data-rate units
- ↑ Wikipedia: Data-rate units
- ↑ Wikipedia: Hertz
- ↑ Wikipedia: Alternating current
- ↑ Wikipedia: Desktop computer
- ↑ Wikipedia: Direct current
- ↑ Wikipedia: Gigabit
- ↑ Wikipedia: Gigabyte
- ↑ Wikipedia: Data-rate units
- ↑ Wikipedia: Hertz
- ↑ Wikipedia: Internet of things
- ↑ Wikipedia: Kilobit
- ↑ Wikipedia: Kilobyte
- ↑ Wikipedia: Data-rate units
- ↑ Wikipedia: Kilobit
- ↑ Wikipedia: Kilobyte
- ↑ Wikipedia: Data-rate units
- ↑ Wikipedia: Hertz
- ↑ Wikipedia: Petabyte
- ↑ Wikipedia: Personal Computer
- ↑ Wikipedia: Terabit
- ↑ Wikipedia: Terabyte
- ↑ Wikipedia: Data-rate units
Components
[edit | edit source]
This lesson introduces internal system components and data storage.
Objectives and Skills
[edit | edit source]Objectives and skills for the components portion of IT Fundamentals certification include:[1]
- Explain the purpose of common internal computing components.
- Motherboard/system board
- Firmware/BIOS
- RAM
- CPU
- ARM
- Mobile phone
- Tablet
- 32-bit
- Laptop
- Workstation
- Server
- 64-bit
- Laptop
- Workstation
- Server
- ARM
- Storage
- Hard drive
- SSD
- GPU
- Cooling
- NIC
- Wired vs. wireless
- On-board vs. add-on card
- Compare and contrast storage types.
- Volatile vs. non-volatile
- Local storage types
- RAM
- Hard drive
- Solid state vs. spinning disk
- Optical
- Flash drive
- Local network storage types
- NAS
- File server
- Cloud storage service
Readings
[edit | edit source]Multimedia
[edit | edit source]- YouTube: Basics of Computing & Processing
- YouTube: Common Internal Computing Components
- YouTube: Storage Types
- YouTube: Chapter 2 - IT Fundamentals+ (FC0-U61) System Hardware
Activities
[edit | edit source]- Run the System Information or List Hardware utility for your operating system:
- Windows: Review Microsoft: Description of Microsoft System Information (Msinfo32.exe) Tool. Run System Information on Windows and observe the System Summary, Hardware Resources, Components, and Software Environment available on the system.
- macOS: Review Apple: About System Information. Run System Information on macOS and observe the hardware available on the system.
- Linux GUI: Review It's FOSS: Check Hardware Information on Linux Graphically With Hardinfo. Use Hardinfo to observe the hardware available on the system.
- Linux CLI: Review Binary Tides: Get hardware information on Linux with lshw command. Search the Internet for how to run the
lshw(List Hardware) utility on your Linux distribution. Run lshw and observe the hardware available on the system.
- Create an inventory list of all internal hardware components in your system. Using your preferred hardware vendor, check the hardware specifications for a new system. How recent is your hardware? Is the same technology still in use on current systems?
- Review the Consumer Reports "Computer Buying Guide". Visit your favorite computer retailer's website and go "shopping" for a new computer or familiarize yourself with the hardware of a computer at PCPartPicker or BuildMyPC and build your own system.
- Search the Internet for either RAM upgrade wizard or RAM upgrade tool. Using one of the vendor options available, test your system to determine how much RAM and what type is installed in your system. How much RAM will your system support? What would it cost to 'max out' your system's RAM?
- Run the hard drive utility for your operating system:
- Windows: Review Microsoft: Overview of Disk Management. Run Disk Management on Windows and observe the disks, volumes, and partitions. Be careful not to make any changes.
- macOS: Review How To Geek: How to Use Your Mac’s Disk Utility to Partition, Wipe, Repair, Restore, and Copy Drives. Run Disk Utility on macOS and observe the available drives, disks, and volumes. Be careful not to make any changes.
- Linux: Review LinuxHint: Gnome Disk Utility. Run Disk Utility on Linux and observe the available disks, partitions, and volumes. Be careful not to make any changes.
- Review MakeUseOf: How to Enter the BIOS on Windows 10 (And Older Versions). Restart your system and access the BIOS configuration screen. Review all options available. Exit and restart the system without saving any configuration changes.
- Check your computer or motherboard manufacturer's web site to see if there are any BIOS or firmware updates available for your system. If there are, research the problems the updates resolve and determine whether or not you want to upgrade your system. If so, be sure to back up your system first, and follow the manufacturer's instructions carefully. In particular, do not remove power during a firmware upgrade process.
Lesson Summary
[edit | edit source]













Internal Computing Components
[edit | edit source]- A motherboard is the main printed circuit board (PCB) found in general purpose computers and other expandable systems. It holds, and allows, communication between many of the crucial electronic components of a system, such as the central processing unit (CPU) and memory, and provides connectors for other peripherals.[2]
- BIOS (Basic Input/Output System) is firmware used to perform hardware initialization during the booting process (power-on startup), and to provide runtime services for operating systems and programs.[3]
- Random-access memory (RAM) is a form of computer memory that can be read and changed in any order, typically used to store working data and machine code.[4]
- A central processing unit (CPU) is the electronic circuitry within a computer that executes instructions that make up a computer program.[5]
- ARM, previously Advanced RISC Machine, is a family of reduced instruction set computing (RISC) architectures for computer processors, configured for various environments.[6] ARM processors are currently used in mobile phones and tablets.
- 32-bit processors support integers, memory addresses, or other data units that are 32 bits (4 octets) wide. A processor with 32-bit memory addresses can directly access at most 4 GiB of byte-addressable memory.[7]
- 64-bit processors support integers, memory addresses, or other data units that are 64 bits (8 octets) wide. In principle, a 64-bit microprocessor can address 16 EiBs (16 × 10246 = 264 = 18,446,744,073,709,551,616 bytes, or about 18.4 exabytes) of memory. However, not all instruction sets, and not all processors implementing those instruction sets, support a full 64-bit virtual or physical address space at this time.[8]
- Most personal computers manufactured since 2005 have included 64-bit processors. Most operating systems released since 2010 have supported 64-bit processors. Recently, software developers have been dropping support for 32-bit systems.[9]
- Computer storage includes both primary and secondary storage. Primary storage is volatile and typically referred to as RAM. Secondary storage non-volatile and is often referred to as a hard drive.[10]
- A graphics processing unit (GPU) is a specialized electronic circuit designed to rapidly manipulate and alter memory to accelerate the creation of images in a frame buffer intended for output to a display device.
- Computer cooling is required to remove the waste heat produced by computer components, to keep components within permissible operating temperature limits. Components that are susceptible to temporary malfunction or permanent failure if overheated include integrated circuits such as central processing units (CPUs), chipset, graphics cards, and hard disk drives.[11]
- Computer cooling systems may be active (power-driven, such as with a fan) or passive (using heat sinks and metal cases), or a combination of both. Active systems primarily use air, but liquid-cooled options are available for some high-end systems.[12]
- A network interface controller (NIC) is a computer hardware component that connects a computer to a computer network.[13] NICs are designed to support either wired or wireless connections, and may be either built into the motherboard or added using an expansion card.
Storage Types
[edit | edit source]- Volatile memory is computer memory that requires power to maintain the stored information; it retains its contents while powered on but when the power is interrupted, the stored data is quickly lost.[14]
- Non-volatile memory (NVM) or non-volatile storage is a type of computer memory that can retrieve stored information even after having been power cycled.[15]
- Random-access memory (RAM) is a form of computer memory that can be read and changed in any order, typically used to store working data and machine code.[16]
- Local secondary storage options includes hard disk drives, solid state drives, optical drives, and flash drives.
- A hard disk drive (HDD), hard disk, hard drive, or fixed disk[b] is an electro-mechanical data storage device that uses magnetic storage to store and retrieve digital data using one or more rigid rapidly rotating platters coated with magnetic material.[17]
- A solid-state drive (SSD) is a solid-state storage device that uses integrated circuit assemblies to store data persistently, typically using flash memory.[18]
- Optical storage uses a laser to store and retrieve data from optical media. Examples of optical media include compact discs (CD) and DVDs.[19]
- A flash drive is a portable computer drive that uses flash memory.[20]
- Local network storage options include network-attached storage (NAS) and file servers.
- Network-attached storage (NAS) is a file-level (as opposed to block-level) computer data storage server connected to a computer network providing data access to a heterogeneous group of clients.[21]
- A file server runs one or more server programs, which share file resources with clients.[22] A file server may be dedicated or non-dedicated. A dedicated server is designed specifically for use as a file server, with workstations attached for reading and writing files.[23]
- Cloud storage is a model of computer data storage in which the digital data is stored in logical pools on one or more physical Internet-based servers, sometimes replicated across multiple locations.[24]
Key Terms
[edit | edit source]- ARM (Advanced RISC Machine)
- A family of reduced instruction set computing (RISC) architectures for computer processors, configured for various environments.[25]
- BIOS (Basic Input/Output System)
- Firmware used to perform hardware initialization during the booting process (power-on startup), and to provide runtime services for operating systems and programs.[26]
- bus
- A communication system that transfers data between components inside a computer, or between computers.[27]
- cache
- A hardware or software component that stores data so that future requests for that data can be served faster.[28]
- chipset
- A set of electronic components in an integrated circuit known as a "Data Flow Management System" that manages the data flow between the processor, memory and peripherals.[29]
- CPU (Central Processing Unit)
- The electronic circuitry within a computer that executes instructions that make up a computer program.[30]
- DDR (Double Data-Rate)
- A computer bus that transfers data on both the rising and falling edges of the clock signal.[31]
- DIMM (Dual Inline Memory Module)
- A series of dynamic random-access memory integrated circuits.[32]
- FRU (Field Replaceable Unit)
- A printed circuit board, part, or assembly that can be quickly and easily removed from a computer or other piece of electronic equipment, and replaced by the user or a technician without having to send the entire product or system to a repair facility.[33]
- form factor
- The specification of a motherboard – the dimensions, power supply type, location of mounting holes, number of ports on the back panel, etc.[34]
- HDD (Hard Disk Drive)
- An electro-mechanical data storage device that uses magnetic storage to store and retrieve digital data using one or more rigid rapidly rotating platters coated with magnetic material.[35]
- GPU (Graphics Processing Unit)
- A specialized electronic circuit designed to rapidly manipulate and alter memory to accelerate the creation of images in a frame buffer intended for output to a display device.[36]
- IOPS (Input/Output Operations Per Second)
- A performance measurement used to characterize secondary computer storage devices.[37]
- NIC (Network Interface Card)
- A computer hardware component that connects a computer to a computer network.[38]
- OEM (Original Equipment Manufacturer)
- A company that produces parts and equipment that may be marketed by another manufacturer.[39]
- PCB (Printed Circuit Board)
- Mechanically supports and electrically connects electrical or electronic components using conductive tracks, pads and other features etched from one or more sheet layers of copper laminated onto and/or between sheet layers of a non-conductive substrate.[40]
- PCI (Peripheral Component Interconnect)
- A local computer bus for attaching hardware devices in a computer.[41]
- PCIe (Peripheral Component Interconnect Express)
- A high-speed serial computer expansion bus standard, designed to replace older bus standards[42]
- PSU (Power Supply Unit)
- A device that supplies electric power to a computer system, converting electric current from a source to the correct voltage, current, and frequency.[43]
- RAID (Redundant Array of Independent Disks)
- A data storage virtualization technology that combines multiple physical disk drive components into one or more logical units for the purposes of data redundancy, performance improvement, or both.[44]
- RAM (Random Access Memory)
- A form of computer memory that can be read and changed in any order, typically used to store working data and machine code.[45]
- ROM (Read-Only Memory)
- A type of non-volatile memory useful for storing firmware.[46]
- SATA (Serial Advanced Technology Attachment)
- A computer bus interface that connects host bus adapters to mass storage devices such as hard disk drives, optical drives, and solid-state drives.[47]
- SSD (Solid State Drive)
- A device that uses integrated circuit assemblies to store data persistently, typically using flash memory.[48]
- VGA (Video Graphics Array or Video Graphics Adapter)
- A graphics standard for video display controllers first introduced with the IBM PS/2 line of computers in 1987.[49]
Assessments
[edit | edit source]- Flashcards: Quizlet: IT Fundamentals - Components
- Quiz: Quizlet: IT Fundamentals - Components
See Also
[edit | edit source]References
[edit | edit source]- ↑ CompTIA: IT Fundamentals (ITF+) Exam Objectives FC0-U61
- ↑ Wikipedia: Motherboard
- ↑ Wikipedia: BIOS
- ↑ Wikipedia: Random-access memory
- ↑ Wikipedia: Central processing unit
- ↑ Wikipedia: ARM architecture
- ↑ Wikipedia: 32-bit computing
- ↑ Wikipedia: 64-bit computing
- ↑ Wikipedia: 64-bit computing
- ↑ Wikipedia: Computer memory
- ↑ Wikipedia: Computer cooling
- ↑ Wikipedia: Computer cooling
- ↑ Wikipedia: Network interface controller
- ↑ Wikipedia: Volatile memory
- ↑ Wikipedia: Non-volatile memory
- ↑ Wikipedia: Random-access memory
- ↑ Wikipedia: Hard disk drive
- ↑ Wikipedia: Solid-state drive
- ↑ Wikipedia: Optical storage
- ↑ Wikipedia: Flash drive
- ↑ Wikipedia: Network-attached storage
- ↑ Wikipedia: Client–server model
- ↑ Wikipedia: File server
- ↑ Wikipedia: Cloud storage
- ↑ Wikipedia: ARM architecture
- ↑ Wikipedia: BIOS
- ↑ Wikipedia: Bus (computing)
- ↑ Wikipedia: Cache (computing)
- ↑ Wikipedia: Chipset
- ↑ Wikipedia: Double data rate
- ↑ Wikipedia: Double data rate
- ↑ Wikipedia: DIMM
- ↑ Wikipedia: Field-replaceable unit
- ↑ Wikipedia: Computer form factor
- ↑ Wikipedia: Hard disk drive
- ↑ Wikipedia: Graphics processing unit
- ↑ Wikipedia: IOPS
- ↑ Wikipedia: Network interface controller
- ↑ Wikipedia: Original equipment manufacturer
- ↑ Wikipedia: Printed circuit board
- ↑ Wikipedia: Conventional PCI
- ↑ Wikipedia: PCI Express
- ↑ Wikipedia: Power supply
- ↑ Wikipedia: RAID
- ↑ Wikipedia: Random-access memory
- ↑ Wikipedia: Read-only memory
- ↑ Wikipedia: Serial ATA
- ↑ Wikipedia: Solid-state drive
- ↑ Wikipedia: Video Graphics Array
Peripherals
[edit | edit source]
This lesson introduces peripheral devices and interfaces.
Objectives and Skills
[edit | edit source]Objectives and skills for the peripherals portion of IT Fundamentals certification include:[1]
- Given a scenario, set up and install common peripheral devices to a laptop/PC.
- Devices
- Printer
- Scanner
- Keyboard
- Mouse
- Camera
- External hard drive
- Speakers
- Display
- Installation types
- Plug-and-play vs. driver installation
- Other required steps
- IP-based peripherals
- Web-based configuration steps
- Devices
- Classify common types of input/output device interfaces.
- Networking
- Wired
- Telephone connector (RJ-11)
- Ethernet connector (RJ-45)
- Wireless
- Bluetooth
- NFC
- Wired
- Peripheral device
- USB
- FireWire
- Thunderbolt
- Bluetooth
- RF
- Graphic device
- VGA
- HDMI
- DVI
- DisplayPort
- Mini DisplayPort
- Networking
Readings
[edit | edit source]Multimedia
[edit | edit source]- YouTube: Peripheral Devices
- YouTube: Input/Output Device Interfaces
- YouTube: Chapter 3 - IT Fundamentals+ (FC0-U61) Device Ports and Peripherals
- YouTube: Chapter 3 - IT Fundamentals+ (FC0-U61) Review Questions
Activities
[edit | edit source]- Practice identifying personal computer hardware and peripherals.
- Create an inventory list of all peripherals available on your system. Include separate categories for input, output, and storage.
- Create an inventory list of all interfaces and connections available on your system. Note which peripherals use each interface type.
- Review CNet: How to Calibrate Your Monitor. Check all monitor settings and adjust if necessary.
- Manage input and display language settings.
- Windows: Review Microsoft: Manage the input and display language settings in Windows 10. Adjust keyboard layout and available languages if necessary.
- macOS: Review Apple: Type in another language on your Mac with input sources. Adjust input sources if necessary.
- Linux: Review Make Tech Easier: How to Change the Keyboard Layout in Linux. Adjust the keyboard layout if necessary.
- Manage pointing-device settings.
- Windows: Review Digital Citizen: How to configure the mouse settings and sensitivity, in Windows 10. Adjust mouse settings if necessary.
- Windows: Review Digital Citizen: How to configure your touchpad in Windows 10. Adjust touchpad settings if necessary.
- macOS: Review iMore: How to change the mouse settings on your Mac. Adjust mouse settings if necessary.
- macOS: Review iMore: How to change the trackpad settings on your Mac. Adjust trackpad settings if necessary.
- Linux: Review Ubuntu: Adjust the speed of the mouse and touchpad. Adjust mouse and touchpad settings if necessary.
- View or install network printers.
- Windows: Review WikiHow: How to Install a Network Printer. Use Devices and Printers to view available printers. Consider adding any discovered printers.
- macOS: Review WikiHow: How to Install a Network Printer. Use Printers and Scanners to view available printers. Consider installing any discovered printers.
- Linux: Review Help Desk Geek: How To Install Almost Any Printer On Ubuntu. Use Printers to view available printers. Consider connecting to any discovered printers.
Lesson Summary
[edit | edit source]








Peripheral Devices
[edit | edit source]- A printer is a peripheral device which makes a persistent representation of graphics or text, usually on paper. While most output is human-readable, bar code printers are an example of an expanded use for printers.[2]
- An image scanner, often abbreviated to just scanner, is a device that optically scans images, printed text, handwriting or an object and converts it to a digital image.[3]
- A computer keyboard is a typewriter-style device which uses an arrangement of buttons or keys to act as mechanical levers or electronic switches and functions as the main input method for computers.[4]
- A computer mouse is a hand-held pointing device that detects two-dimensional motion relative to a surface. This motion is typically translated into the motion of a pointer on a display, which allows a smooth control of the graphical user interface of a computer.[5]
- A webcam is a video camera that feeds or streams an image or video in real time to or through a computer to a computer network, such as the Internet.[6]
- External hard disk drives typically connect to a computer via USB. Plug and play drive functionality offers system compatibility and features large storage options and portable design.[7]
- Computer speakers are speakers sold for use with computers. Most such speakers have an internal amplifier and consequently require a power source, which may be by a mains power supply often via an AC adapter, batteries, or a USB port. The signal input connector is often a 3.5 mm jack plug (usually color-coded lime green per the PC 99 standard).[8]
- A computer monitor is an output device that displays information in pictorial form. A monitor usually comprises the visual display, circuitry, casing, and power supply. The display device in modern monitors is typically a thin film transistor liquid crystal display (TFT-LCD) with LED backlighting.[9]
Installation Types
[edit | edit source]Peripheral installation options include "plug-and-play", network (IP-based) peripherals, and web-based configuration. Other configuration steps may be required after the initial connection is made.
- A plug and play (PnP) device or computer bus is one with a specification that facilitates the discovery of a hardware component in a system without the need for physical device configuration or user intervention in resolving resource conflicts.[10]
- If plug-and-play fails to properly detect a device, or no device driver can be found, it may be necessary to install peripheral support software or device drivers manually.
- Installed peripherals will have a default configuration. After installation, it may be necessary to access a configuration page to customize settings for your environment.
- Configuring network (IP-based) peripherals often requires locating the device's IP address and then using a web browser to navigate to that IP address. Other peripherals will have custom software that can search the network for devices to be configured.
Device Interfaces
[edit | edit source]









- RJ-11 is a 6 position 2, 4 or 6 contact modular connector typically used for phone cable connections[11]
- RJ-45 is an 8 position 8 contact modular connector typically used for network cable connections.[12]
- Bluetooth is a wireless technology standard used for exchanging data between fixed and mobile devices over short distances using short-wavelength UHF radio waves and building personal area networks (PANs). The most common range for Bluetooth communication is up to 10 meters.[13]
- NFC (Near Field Communications) is a set of communication protocols for communication between two electronic devices over a distance of 4 cm (11⁄2 in) or less.[14]
- USB (Universal Serial Bus) is an industry standard that defines the cables, connectors and communications protocols used in a bus for connection, communication, and power supply between computers and electronic devices communicating at 12 Mbps, 480 Mbps, or 5 Gbps.[15]
- FireWire (IEEE 1394) is an interface standard for a serial bus for high-speed communications and isochronous real-time data transfer developed by Apple and replaced with Thunderbolt.[16]
- Thunderbolt is a hardware interface that allows for the connection of external peripherals to a computer, combining PCI Express (PCIe) and DisplayPort (DP) into one serial signal alongside a DC connection for electric power, and transmitted over one cable, most often used for video and other high-speed connections on Apple computers.[17]
- RF (Radio Frequency) uses the oscillation rate of an alternating electric current or voltage or of a magnetic, electric or electromagnetic field or mechanical system in the frequency range from around 20 kHz to around 300 GHz for wireless peripheral communications.[18]
- Video Graphics Array (VGA) is a graphics standard for video display controller first introduced with the IBM PS/2 line of computers in 1987. Through widespread adoption, the term has also come to mean either an analog computer display standard, the 15-pin D-subminiature VGA connector, or the 640×480 resolution characteristic of the VGA hardware.[19]
- HDMI (High-Definition Media Interface) is a proprietary audio/video interface for transferring uncompressed video data and compressed or uncompressed digital audio data from a compliant source device to a compatible computer monitor, video projector, digital television, or digital audio device.[20]
- DVI (Digital Visual Interface) is a 29-pin digital video display interface used to connect a video source to a display device.[21]
- DisplayPort (DP) is a digital display interface developed by a consortium of PC and chip manufacturers and standardized by the Video Electronics Standards Association (VESA). The interface is primarily used to connect a video source to a display device such as a computer monitor, and it can also carry audio, USB, and other forms of data.[22]
- Mini DisplayPort is a miniaturized version of the DisplayPort audio-visual digital interface used on Apple Macintosh computers. Mini DisplayPort uses the same plug form factor as Thunderbolt. In 2016 Apple began phasing out this port and replacing it with USB-C connectors. The Mini DisplayPort is also fitted to some PC motherboards, and some PC notebooks from Asus, Microsoft, MSI, Lenovo, Toshiba, HP, Dell, and other manufacturers.[23]
Key Terms
[edit | edit source]- BD-ROM (Blu-ray Disc-Read-Only Memory)
- A digital optical disc data storage format designed to supersede the DVD format, with a storage capacity of 25 GB per layer, and dual layer discs (50 GB) being the industry standard for high definition (1080p) feature-length video discs.[24]
- CD (Compact Disc)
- A digital optical disc data storage format originally developed to store and play only sound recordings (CD-DA), but was later adapted for storage of data (CD-ROM), with a storage capacity of 737 MB.[25]
- CD-ROM (Compact Disc-Read-Only Memory)
- A pre-pressed optical compact disc which contains data and is not writable or erasable.[26]
- CD-RW (Compact Disc-Rewritable)
- A compact disc that can be written, read arbitrarily many times, erased and written again.[27]
- DVD (Digital Video Disc or Digital Versatile Disc)
- A digital optical disc storage format with a storage capacity of 4.7 GB for a single-layered, single-sided disc and 8.5 GB for a dual-layered, single-sided disc.[28]
- DVD-R (Digital Video Disc-Recordable)
- A DVD that typically has a storage capacity of 4.7 GB and can be written once and read arbitrarily many times.[29]
- DVD-RW (Digital Video Disc-Rewritable)
- A rewritable optical disc with equal storage capacity to a DVD-R, typically 4.7 GB, that stores data in one long spiral track.[30][31]
- DVI (Digital Visual Interface)
- A digital video display interface used to connect a video source to a display device.[32]
- eSATA (External Serial Advanced Technology Attachment)
- Provides a variant of SATA meant for external connectivity with a more robust connector, longer shielded cables, and stricter electrical standards.[33]
- HDMI (High-Definition Media Interface)
- A proprietary audio/video interface for transferring uncompressed video data and compressed or uncompressed digital audio data from a compliant source device to a compatible computer monitor, video projector, digital television, or digital audio device.[34]
- IR (Infrared)
- A class of devices employing an optical portion of the electromagnetic spectrum for wireless communications, commonly found in consumer electronics devices such as television remote controls, PDAs, laptops, and computers.[35]
- NAS (Network Attached Storage)
- A file-level computer data storage server connected to a computer network providing data access to a heterogeneous group of clients.[36]
- NFC (Near Field Communications)
- A set of communication protocols for communication between two electronic devices over a distance of 4 cm (11⁄2 in) or less.[37]
- RF (Radio Frequency)
- The oscillation rate of an alternating electric current or voltage or of a magnetic, electric or electromagnetic field or mechanical system in the frequency range from around 20 kHz to around 300 GHz.[38]
- RJ (Registered Jack)
- A standardized telecommunication network interface for connecting voice and data equipment to a service provided by a local exchange carrier or long distance carrier.[39]
- RJ-11 (Registered Jack Function 11)
- A 6 position 2, 4 or 6 contact modular connector typically used for phone cable connections[40]
- RJ-45 (Registered Jack Function 45)
- An 8 position 8 contact modular connector typically used for network cable connections.[41]
- SD Card (Secure Digital Card)
- A nonvolatile memory card used extensively in portable devices, such as mobile phones, digital cameras, GPS navigation devices, handheld consoles, and tablet computers.[42]
- UPS (Uninterruptable Power Supply)
- An uninterruptible power supply, also uninterruptible power source, UPS or battery/flywheel backup, is an electrical apparatus that provides emergency power to a load when the input power source, typically main power, fails.[43]
- USB (Universal Serial Bus)
- An industry standard that defines the cables, connectors and communications protocols used in a bus for connection, communication, and power supply between computers and electronic devices communicating at 12 Mbps, 480 Mbps, or 5 Gbps.[44]
Assessments
[edit | edit source]- Flashcards: Quizlet: IT Fundamentals - Peripherals
- Quiz: Quizlet: IT Fundamentals - Peripherals
See Also
[edit | edit source]References
[edit | edit source]- ↑ CompTIA: IT Fundamentals (ITF+) Exam Objectives FC0-U61
- ↑ Wikipedia: Printer (computing)
- ↑ Wikipedia: Image scanner
- ↑ Wikipedia: Computer keyboard
- ↑ Wikipedia: Computer mouse
- ↑ Wikipedia: Webcam
- ↑ Wikipedia: Hard disk drive
- ↑ Wikipedia: Computer speakers
- ↑ Wikipedia: Computer monitor
- ↑ Wikipedia: Plug and play
- ↑ Wikipedia: Registered jack
- ↑ Wikipedia: Registered jack
- ↑ Wikipedia: Bluetooth
- ↑ Wikipedia: Near-field communication
- ↑ Wikipedia: USB
- ↑ Wikipedia: Firewire
- ↑ Wikipedia: Thunderbolt (interface)
- ↑ Wikipedia: Radio frequency
- ↑ Wikipedia: Video Graphics Array
- ↑ Wikipedia: HDMI
- ↑ Wikipedia: Digital Video Interface
- ↑ Wikipedia: DisplayPort
- ↑ Wikipedia: Mini DisplayPort
- ↑ Wikipedia: Blu-ray Disc
- ↑ Wikipedia: Compact disc
- ↑ Wikipedia: CD-ROM
- ↑ Wikipedia: CD-RW
- ↑ Wikipedia: DVD
- ↑ Wikipedia: DVD-R
- ↑ Wikipedia: DVD-RW
- ↑ Wikipedia: DVD-RAM
- ↑ Wikipedia: Digital Video Interface
- ↑ Wikipedia: eSATA
- ↑ Wikipedia: HDMI
- ↑ Wikipedia: Consumer IR
- ↑ Wikipedia: Network-attached storage
- ↑ Wikipedia: Near-field communication
- ↑ Wikipedia: Radio frequency
- ↑ Wikipedia: Registered jack
- ↑ Wikipedia: Registered jack
- ↑ Wikipedia: Registered jack
- ↑ Wikipedia: Secure Digital
- ↑ Wikipedia: Uninterruptible power supply
- ↑ Wikipedia: USB
Operating Systems
[edit | edit source]
This lesson introduces operating systems and file systems.
Objectives and Skills
[edit | edit source]Objectives and skills for the operating systems portion of IT Fundamentals certification include:[1]
- Explain the purpose of operating systems.
- Interface between applications and hardware
- Disk management
- Process management/scheduling
- Kill process/end task
- Application management
- Memory management
- Device management
- Access control/protection
- Types of OS
- Mobile device OS
- Workstation OS
- Server OS
- Embedded OS
- Firmware
- Hypervisor (Type 1)
- Compare and contrast components of an operating system.
- File systems and features
- File systems
- NTFS
- FAT32
- HFS
- Ext4
- File systems
- Features
- Compression
- Encryption
- Permissions
- Journaling
- Limitations
- Naming rules
- File management
- Folders/directories
- File types and extensions
- Permissions
- Services
- Processes
- Drivers
- Utilities
- Task scheduling
- Interfaces
- Console/command line
- GUI
- File systems and features
Readings
[edit | edit source]Multimedia
[edit | edit source]- YouTube: Purpose of Operating Systems
- YouTube: Components of an Operating System
- YouTube: Chapter 5 - IT Fundamentals+ (FC0-U61) Understanding Operating Systems
Activities
[edit | edit source]- Perform system updates:
- Windows: Review Microsoft: Windows Update. Run Windows Update and install any missing critical updates.
- macOS: Review Apple: How to update the software on your Mac. Check for software updates and install any missing updates.
- Linux: Review Linux.com: Updating Your System. Check for system updates and install any missing updates.
- Chromium OS: Review Google: Update your Chromebook operating system. Check for system updates and install any missing updates.
- Update device drivers.
- Windows: Review Wikipedia: Device Manager and Microsoft: Update drivers in Windows 10. Run Device Manager on a Windows system. Use Device Manager to check for updated drivers for all display adapters, network adapters, and sound controllers.
- macOS: Review Apple: How to update the software on your Mac. Use Software Update to update software on your system.
- Linux: Review How-To Geek: How to Install Hardware Drivers on Linux. Run Software & Updates and check to see if any additional drivers are in use and update if necessary.
- Use your system's monitoring utilities to review active processes and resources in use.
- Windows: Review Wikipedia: Task Manager (Windows) and Wikipedia: Resource Monitor and run both utilities. Check for any processes unexpectedly using system resources.
- macOS: Review Wikipedia: Activity Monitor and run the utility. Check for any processes unexpectedly using system resources.
- Linux: Review GNOME: System Monitor and run the utility. Check for any processes unexpectedly using system resources.
- Terminate a running application.
- Windows: Review Bleeping Computer: How to close a program using Task Manager. Start a program such as Notepad or Calculator and use Task Manager to terminate the program.
- macOS: Review How to force an app to quit on your Mac. Start a program such as TextEdit or Calculator and use Force Quit Applications to terminate the program.
- Linux: Review It's FOSS: Use Task Manager Equivalent in Linux. Use System Monitor to review running processes in Linux.
- Examine system health and recent events for your system:
- Windows: Review Wikipedia: Event Viewer and run the utility. Review recent events for potential issues or concerns.
- macOS: Review Wikipedia: Console (OS X) and run the utility. Review recent events for potential issues or concerns.
- Linux: Review Lifewire: An Introduction to Linux Log Files and view the system logs. Review recent events for potential issues or concerns.
- Manage folders and files.
- Windows: Review GCF Global: Windows Basics - Working with Files. Review the existing structure and properties for the Documents folder. Improve file organization, if necessary.
- macOS: Review GCF Global: macOS Basics - Working with Files. Review the existing structure and information for the Documents folder. Improve file organization, if necessary.
- Linux: Review IBM: Learn Linux, 101: File and directory management. Review the existing structure and detailed information for the Documents folder. Improve file organization, if necessary.
- Schedule a task to run automatically.
- Windows: Review Windows Central: How to create an automated task using Task Scheduler on Windows 10. Schedule a task to automatically run the calculator five minutes from now. Remove the task after it runs.
- macOS: Review Medium: How to Use launchd to Run Services in macOS. Use launchd to automatically run the calculator five minutes from now. Unload the job after it runs.
- Linux: Review How To Geek: How to Schedule Tasks on Linux: An Introduction to Crontab Files. Schedule a task to automatically run the calculator five minutes from now. Remove the task after it runs.
- Test other operating systems using your web browser:
- All: OnWorks: Free Online Workstations
- Windows: MIT: Windows 10 Simulator
- macOS: alessioatzeni.com: Mac OSX Lion CSS3 - password is
admin - Linux: Test different Linux distributions using distrotest.net. Popular Linux desktop distributions include Ubuntu, Linux Mint, and Fedora.
- Download and install virtualization software for your system. Use it to test other operating systems. This activity will also help you test databases in a future lesson.
- Windows: Microsoft Hyper-V, Oracle VirtualBox, or VMware Player.
- OS X: Oracle VirtualBox, Parallels, or VMware Fusion.
- Linux: Oracle VirtualBox or VMware Player.
Lesson Summary
[edit | edit source]Operating System Concepts
[edit | edit source]





- An operating system (OS) is system software that manages computer hardware, software resources, and provides common services for computer programs. For hardware functions such as input and output and memory allocation, the operating system acts as an intermediary between programs and the computer hardware.[2]
- Access to data stored on disks is a central feature of all operating systems. Computers store data on disks using files, which are structured in specific ways in order to allow for faster access, higher reliability, and to make better use of the drive's available space. The specific way in which files are stored on a disk is called a file system, and enables files to have names and attributes. It also allows them to be stored in a hierarchy of directories or folders arranged in a directory tree.[3]
- Multitasking refers to the running of multiple independent computer programs on the same computer; giving the appearance that it is performing the tasks at the same time. Since most computers can do at most one or two things at one time, this is generally done via time-sharing, which means that each program uses a share of the computer's time to execute.[4]
- An operating system kernel contains a scheduling program which determines how much time each process spends executing, and in which order execution control should be passed to programs. Control is passed to a process by the kernel, which allows the program access to the CPU and memory. Later, control is returned to the kernel through some mechanism, so that another program may be allowed to use the CPU. This so-called passing of control between the kernel and applications is called a context switch. Modern operating systems have preemptive control over running applications, device drivers, and kernel code.[5]
- Preemptive multitasking allows the operating system to terminate running processes that stop responding. Different operating systems refer to this capability by different names, such as ending tasks or killing processes.[6]
- Modern CPUs support multiple modes of operation. CPUs with this capability offer at least two modes: user mode and supervisor mode. Supervisor mode is used by the kernel for low level tasks that need unrestricted access to hardware, such as controlling how memory is accessed, and communicating with devices such as disk drives and video display devices. User mode, in contrast, is used for almost everything else. Application programs, such as word processors and database managers, operate within user mode, and can only access machine resources by turning control over to the kernel, a process which causes a switch to supervisor mode.[7]
- Among other things, a multiprogramming operating system kernel must be responsible for managing all system memory which is currently in use by programs. This ensures that a program does not interfere with memory already in use by another program. Since programs time share, each program must have independent access to memory.[8]
- Modern operating systems must be capable of distinguishing between requests which should be allowed to be processed, and others which should not be processed. Systems commonly have some form of requester identity, such as a user name, and to establish identity there may be a process of authentication such as a password, ID card, and/or biometric data.[9]
- Once authenticated, user access to resources must be authorized by verifying that the requester has permission to access the resource. Authorization permissions typically include separate options for read, create, modify, and delete.[10]
- Resource permissions may be granted directly to users, or permissions may be granted to groups of users, and user accounts are added to various administrative groups to inherit permissions.[11]
- Operating system resource management may also include auditing options. These would allow tracking of requests for access to resources (such as, "who has been reading this file?"). Internal security, or security from an already running program is only possible if all possibly harmful requests must be carried out through interrupts to the operating system kernel. If programs can directly access hardware and resources, they cannot be secured.[12]
Operating System Types
[edit | edit source]


- A mobile operating system (or mobile OS) is an operating system for mobile phones, tablets, smartwatches, 2-in-1 PCs (that can be convert to a laptop mode or detach and work as a tablet mode) or other mobile devices. While computers such as typical laptops are 'mobile', the operating systems usually used on them are not considered mobile ones, as they were originally designed for desktop computers that historically did not have or need specific mobile features. This distinction is becoming blurred in some newer operating systems that are hybrids made for both uses.[13]
- Desktop or workstation operating systems manage computer hardware, software resources, and provides common services for personal computer programs. Popular workstation operating systems include Microsoft Windows, Apple macOS, and various Linux distributions.[14]
- Server operating systems provide functionality for other programs or devices, called "clients". Common server use includes application servers, communication servers, computing servers, database servers, file servers, mail servers, media servers, print servers, virtual servers, and web servers. Popular server operating systems include Linux and Windows Server.[15]
- An embedded operating system is an operating system for embedded computer systems, a combination of a computer processor, computer memory, and input/output peripheral devices—that has a dedicated function within a larger mechanical or electrical system. This type of operating system is typically designed to be resource-efficient and reliable.[16][17]
- Firmware is a specific class of computer software that provides the low-level control for a device's specific hardware. Firmware can either provide a standardized operating environment for more complex device software, or, for less complex devices, act as the device's complete operating system, performing all control, monitoring and data manipulation functions.[18]
- A hypervisor (or virtual machine monitor, VMM) is computer software, firmware or hardware that creates and runs virtual machines. A computer on which a hypervisor runs one or more virtual machines is called a host machine, and each virtual machine is called a guest machine. The hypervisor presents the guest operating systems with a virtual operating platform and manages the execution of the guest operating systems.[19]
- Type-1, native or bare-metal hypervisors run directly on the host's hardware to control the hardware and to manage guest operating systems. Type-2 or hosted hypervisors run on a conventional operating system (OS) just as other computer programs do.[20]
File Systems
[edit | edit source]




A file system or filesystem (often abbreviated to fs), controls how data is stored and retrieved.[21]
- NTFS (New Technology File System) a proprietary journaling file system developed by Microsoft, for use with Windows NT and later Windows operating systems.[22]
- FAT32 (32-bit File Allocation Table) is a legacy industry-standard computer file system with support for an increased number of possible clusters compared to previous versions.[23]
- HFS (Hierarchical File System) is a proprietary file system developed by Apple Inc. in 1998 for use in computer systems running macOS.[24]
- APFS (Apple File System) is a proprietary file system released in 2017 for macOS, optimized for flash and solid-state drive storage, with a primary focus on encryption.[25]
- ext (extended file system) is a file system created specifically for the Linux kernel. ext4 is the fourth version of this file system.[26]
File system features include:
- Compression is the process of encoding information using fewer bits than the original representation.[27]
- Encryption is the process of encoding a message or information in such a way that only authorized parties can access it and those who are not authorized cannot.[28]
- Permissions provide access rights to specific users and groups of users. These permissions control the ability of the users to view, change, navigate, and execute the contents of the file system.[29]
- Journaling keeps track of changes not yet committed to the file system's main part by recording the intentions of such changes in a data structure known as a "journal", which is usually a circular log. In the event of a system crash or power failure, such file systems can be brought back online more quickly with a lower likelihood of becoming corrupted.[30]
- Not all file systems support all features. For example, the FAT32 file system doesn't support compression, encryption, permissions, or journaling.[31]
- File systems often have restrictions on file names, such file name length and use of special characters in the name. There may also be special meaning given to specific characters, such as using a leading period (.) to indicate a hidden file or a tilde (~) for a temporary system file.
File management includes directories (folders), file types and extensions, and permissions.
- A directory is a file system cataloging structure which contains references to other computer files, and possibly other directories. On some file systems, directories are known as folders.[32]
- A file format is a standard way that information is encoded for storage in a computer file. It specifies how bits are used to encode information in a digital storage medium. Different operating systems have traditionally taken different approaches to determining a particular file's format, with each approach having its own advantages and disadvantages.[33]
- A popular method used by many operating systems, including Windows, macOS, CP/M, DOS, VMS and VM/CMS is to determine the format of a file based on the end of its name, more specifically the letters following the final period. This is known as the filename extension.[34]
- Another way of storing the format of a file is to explicitly store information about the format in the file system, rather than within the file or file name itself. This is known as external metadata.[35]
- An access-control list (ACL) is a list of permissions attached to an object. An ACL specifies which users or system processes are granted access to objects, as well as what operations are allowed on given objects.[36]
Operating System Components
[edit | edit source]
- A service, also known as a daemon, is a computer program that runs as a background process, rather than being under the direct control of an interactive user. Systems often start daemons at boot time which will respond to network requests, hardware activity, or other programs by performing some task.[37]
- A process is the instance of a computer program that is being executed by one or many threads. It contains the program code and its activity. Depending on the operating system (OS), a process may be made up of multiple threads of execution that execute instructions concurrently.[38]
- A device driver is a computer program that operates or controls a particular type of device that is attached to a computer. A driver provides a software interface to hardware devices, enabling operating systems and other computer programs to access hardware functions without needing to know precise details about the hardware being used.[39]
- Utility software is software designed to help to analyze, configure, optimize or maintain a computer. It is used to support the computer infrastructure - in contrast to application software, which is aimed at directly performing tasks that benefit ordinary users. Common utility categories include system, storage device management, and file management.[40]
- A task or job scheduler is a computer application or service for controlling unattended background program execution of tasks. Modern task schedulers typically provide a graphical user interface and a single point of control for definition and monitoring of background executions in a distributed network of computers.[41]
Operating System User Interfaces
[edit | edit source]

- A CLI (Command Line Interface) is a type of interface that processes commands to a computer program in the form of lines of text.[42]
- A GUI (Graphical User Interface) is a form of user interface that allows users to interact with electronic devices through graphical icons.[43]
Key Terms
[edit | edit source]
- APFS (Apple File System)
- A proprietary file system released in 2017 for macOS, optimized for flash and solid-state drive storage, with a primary focus on encryption.[44]
- CLI (Command Line Interface)
- A type of interface that processes commands to a computer program in the form of lines of text.[45]
- ext (extended file system)
- A file system created specifically for the Linux kernel.[46]
- FAT (File Allocation Table)
- A legacy computer file system architecture and a family of industry-standard file systems utilizing it.[47]
- FAT32 (32-bit File Allocation Table)
- An updated legacy computer file system which supports an increased number of possible clusters.[48]
- HFS (Hierarchical File System)
- A proprietary file system developed by Apple Inc. in 1998 for use in computer systems running macOS.[49]
- GUI (Graphical User Interface)
- A form of user interface that allows users to interact with electronic devices through graphical icons.[50]
- kernel
- A computer program at the core of a computer's operating system with complete control over everything in the system.[51]
- NTFS (New Technology File System)
- A proprietary journaling file system developed by Microsoft, for use with Windows NT and later Windows operating systems.[52]
- OS (Operating System)
- System software that manages computer hardware and software resources and provides common services for computer programs.[53]
Assessments
[edit | edit source]- Flashcards: Quizlet: IT Fundamentals - Operating Systems
- Quiz: Quizlet: IT Fundamentals - Operating Systems
See Also
[edit | edit source]References
[edit | edit source]- ↑ CompTIA: IT Fundamentals (ITF+) Exam Objectives FC0-U61
- ↑ Wikipedia: Operating system
- ↑ Wikipedia: Operating system
- ↑ Wikipedia: Operating system
- ↑ Wikipedia: Operating system
- ↑ Wikipedia: Operating system
- ↑ Wikipedia: Operating system
- ↑ Wikipedia: Operating system
- ↑ Wikipedia: Operating system
- ↑ Wikipedia: Operating system
- ↑ Wikipedia: Operating system
- ↑ Wikipedia: Operating system
- ↑ Wikipedia: Mobile operating system
- ↑ Wikipedia: Operating system
- ↑ Wikipedia: Server (computing)
- ↑ Wikipedia: Embedded operating system
- ↑ Wikipedia: Embedded system
- ↑ Wikipedia: Firmware
- ↑ Wikipedia: Hypervisor
- ↑ Wikipedia: Hypervisor
- ↑ Wikipedia: File system
- ↑ Wikipedia: NTFS
- ↑ Wikipedia: File Allocation Table
- ↑ Wikipedia: Hierarchical File System
- ↑ Wikipedia: Apple File System
- ↑ Wikipedia: Extended file system
- ↑ Wikipedia: Data compression
- ↑ Wikipedia: Encryption
- ↑ Wikipedia: File system permissions
- ↑ Wikipedia: Journaling file system
- ↑ Wikipedia: File system
- ↑ Wikipedia: Directory (computing)
- ↑ Wikipedia: File format
- ↑ Wikipedia: File format
- ↑ Wikipedia: File format
- ↑ Wikipedia: Access-control list
- ↑ Wikipedia: Daemon (computing)
- ↑ Wikipedia: Process (computing)
- ↑ Wikipedia: Device driver
- ↑ Wikipedia: Utility software
- ↑ Wikipedia: Job scheduler
- ↑ Wikipedia: Command-line interface
- ↑ Wikipedia: Graphical user interface
- ↑ Wikipedia: Apple File System
- ↑ Wikipedia: Command-line interface
- ↑ Wikipedia: Extended file system
- ↑ Wikipedia: File Allocation Table
- ↑ Wikipedia: File Allocation Table
- ↑ Wikipedia: Hierarchical File System
- ↑ Wikipedia: Graphical user interface
- ↑ Wikipedia: Kernel (operating system)
- ↑ Wikipedia: NTFS
- ↑ Wikipedia: Operating system
Applications
[edit | edit source]
This lesson introduces software applications, licensing, and installation.
Objectives and Skills
[edit | edit source]Objectives and skills for the applications portion of IT Fundamentals certification include:[1]
- Explain the purpose and proper use of software.
- Productivity software
- Word processing software
- Spreadsheet software
- Presentation software
- Web browser
- Visual diagramming software
- Collaboration software
- Email client
- Conferencing software
- Instant messaging software
- Online workspace
- Document sharing
- Business software
- Database software
- Project management software
- Business-specific applications
- Accounting software
- Productivity software
- Compare and contrast general application concepts and uses.
- Single-platform software
- Cross-platform software
- Compatibility concerns
- Licensing
- Single use
- Group use/site license
- Concurrent license
- Open source vs. proprietary
- Subscription vs. one-time purchase
- Product keys and serial numbers
- Software installation best practices
- Reading instructions
- Reading agreements
- Advanced options
- Explain methods of application architecture and delivery models.
- Application delivery methods
- Locally installed
- Network not required
- Application exists locally
- Files saved locally
- Local network hosted
- Network required
- Internet access not required
- Cloud hosted
- Internet access required
- Service required
- Files saved in the cloud
- Locally installed
- Application architecture models
- One tier
- Two tier
- Three tier
- n-tier
- Application delivery methods
Readings
[edit | edit source]- Wikipedia: Productivity software
- Wikipedia: Collaboration software
- Wikipedia: Software license
- Wikipedia: Installation (computer programs)
- Wikipedia: Multitier architecture
Multimedia
[edit | edit source]- YouTube: Purpose & Proper Use of Software
- YouTube: General Application Concepts & Uses
- YouTube: LibreOffice vs. Microsoft Office
- YouTube: Methods of Application Architecture & Delivery Models
- YouTube: Chapter 9 - IT Fundamentals+ (FC0-U61) Using and Managing Application Software
Activities
[edit | edit source]- Use your operating system's built-in text editor to create and edit text files:
- Windows: Review Microsoft: Open Notepad. Use Notepad to create a text file and save it under Documents.
- macOS: Review Apple: Mac Basics: TextEdit. Use TextEdit to create a text file and save it under Documents.
- Linux: Review Wikipedia: gedit or Wikipedia: GNU nano. Use gedit or nano to create a text file and save it under Documents.
- Use productivity software.
- Review Wikipedia: LibreOffice.
- Download and install LibreOffice.
- Review LibreOffice.org: Documentation.
- Use the open source software suite to create a short document, spreadsheet, and presentation. Save the files under Documents.
- Use screen sharing software to collaborate with other users:
- Windows: Search the Internet for information on Chrome Remote Desktop, Microsoft Remote Desktop, TeamViewer, or similar applications. Use one of these applications to share your desktop with another user.
- macOS: Search the Internet for information on Chrome Remote Desktop, Microsoft Remote Desktop, TeamViewer, or similar applications. Use one of these applications to share your desktop with another user.
- Linux: Search the Internet for information on Chrome Remote Desktop, Microsoft Remote Desktop, TeamViewer, or similar applications. Use one of these applications to share your desktop with another user.
- Use video conferencing software to collaborate with other users:
- Windows: Search the Internet for information on Skype, Google Hangouts, Facebook Messenger, Zoom, or similar applications. Use one of these applications to set up and join a video conference to collaborate with other users.
- macOS: Search the Internet for information on Facetime, Skype, Google Hangouts, Facebook Messenger, Zoom, or similar applications. Use one of these applications to set up and join a video conference to collaborate with other users.
- Linux: Search the Internet for information on Skype, Google Hangouts, Facebook Messenger, Zoom, or similar applications. Use one of these applications to set up and join a video conference to collaborate with other users.
- Use cloud-hosted applications and storage.
- Use Amazon AppStream to run OpenOffice apps in the cloud using your browser. Create a short document, spreadsheet, and presentation. Save the files to a cloud storage provider account (Google Drive, OneDrive, iCloud, etc.).
- Compare licensing and distribution approaches for different productivity software suites. Include Microsoft Office and either LibreOffice or OpenOffice. Consider platforms, cost, open source vs. proprietary, subscription vs. purchase, and the use of product keys.
Lesson Summary
[edit | edit source]Productivity Software
[edit | edit source]




Productivity software is used for producing information such as documents, presentations, worksheets, data, charts, graphs, digital paintings, electronic music and digital video).[2]
- Word processing software provides for input, editing, formatting and output of text, often with some additional features.[3]
- Spreadsheet software is used for organization, analysis and storage of data entered in cells of a table. Each cell may contain either numeric or text data, or the results of formulas that automatically calculate and display a value based on the contents of other cells.[4]
- Presentation software is used to display information in the form of a slide show. It has three major functions: an editor that allows text to be inserted and formatted, a method for inserting and manipulating graphic images, and a slide-show system to display the content.[5]
- Web browser is used for accessing information on the World Wide Web. When a user requests a particular website, the web browser retrieves the necessary content from a web server and then displays the resulting web page on the user's device.[6]
- Visual diagramming software is used to create vector graphics with points connected by lines and curves to form polygons and other shapes.[7]
Collaboration Software
[edit | edit source]
Collaboration software is application software designed to help people working on a common task to attain their goals.[8]
- Email client is used to access and manage a user's email.[9]
- Conferencing software is used to facilitate webinars ("web seminars"), webcasts, and peer-level web meetings.[10]
- Instant messaging software is used to facilitate a type of online chat that offers real-time text transmission over the Internet.[11]
- Online workspaces provide an environment that supports application delivery, data, management, security, and a consistent user experience across a variety of devices.[12]
- Document sharing systems help multiple people work together at the same time on a single document or file to achieve a single final version.[13]
Business Software
[edit | edit source]

Business software is any software or set of computer programs used by business users to perform various business functions.[14]
- Database software provides various functions that allow entry, storage and retrieval of large quantities of information and provides ways to manage how that information is organized.[15]
- Project management software is used to help plan, organize, and manage resource tools and develop resource estimates for sequences of events or tasks.[16][17]
- Business-specific applications include any software or set of computer programs developed for and customized to a specific business or industry's needs.[18]
- Accounting software records and processes accounting transactions within functional modules such as accounts payable, accounts receivable, journal, general ledger, payroll, and trial balance.[19]
Platform
[edit | edit source]
A computing platform is the environment in which a piece of software is executed. It may be the hardware or the operating system (OS), even a web browser and associated application programming interfaces, or other underlying software.[20]
- Single-platform software is implemented on a specific operating system and CPU architecture, such as Microsoft Windows and x64 architecture.[21]
- Cross-platform software is implemented on multiple computing platforms. For example, a cross-platform application may run on Microsoft Windows, Linux, and macOS.[22]
- Cross-platform software development challenges include testing, lowest-common-denominator feature options, different user interface conventions, and performance issues.[23]
License
[edit | edit source]
A software license is a legal instrument (usually by way of contract law, with or without printed material) governing the use or redistribution of software.[24]
- Single use allows use by a single user and/or a single computer.[25]
- Group use/site license allows use by a department or organization at a given geographic location.[26]
- Concurrent licenses allow use by a given number of users at the same time.[27]
- An open-source license allows the source code, blueprint or design to be used, modified and/or shared under defined terms and conditions.[28]
- Proprietary software, also known as closed-source software, is non-free computer software for which the software's publisher or another person retains intellectual property rights.[29]
- Perpetual licenses are permanent. Perpetual licenses may require annual maintenance subscriptions for updates.[30]
- Subscription-only licenses must be renewed at the end of each subscription period, typically annually.[31]
- A product key is a specific software-based key for a computer program. It certifies that the copy of the program is original. Activation is sometimes done offline by entering the key or online activation may be required to prevent multiple people using the same key.[32]
Installation
[edit | edit source]Installation (or setup) of a computer program (including device drivers and plugins), is the act of making the program ready for execution. Installation options include:[33]
- Attended installation is performed by a user manually running the installation program and selecting desired options.
- Silent installation is performed without any user interface updates.
- Unattended installation is performed without user interaction.
- Headless installation is performed without a computer monitor connected.
- Scheduled installation is performed at a specific time or in response to a given condition.
- Clean installation is performed on a system without old versions of the program being present. For operating systems, a clean installation is performed on an erased partition.
- Network installation is performed from a shared network resource.
Hosting
[edit | edit source]
- Installation typically involves code (program) being copied/generated from the installation files to new files on the local computer for easier access by the operating system, creating necessary directories, registering environment variables, providing separate program for un-installation etc.[34]
- Because code is generally copied/generated in multiple locations, uninstallation usually involves more than just erasing the program folder. For example, registry files and other system code may need to be modified or deleted for a complete uninstallation.
- Network hosting involves installing the application on a shared network resource. Client computers require network access to run the program from the shared resource.[35]
- Software as a service (SaaS) is a software licensing and delivery model in which software is licensed on a subscription basis and is centrally hosted on Internet-based servers.[36]
Architecture
[edit | edit source]
Software architecture refers to the fundamental structures of a software system.[37]
- Single-tier software has all parts of the program designed to run on the local computer.[38]
- Two-tier software, also known as a client-server architecture, has a front-end presentation layer providing the user interface and a back end layer providing the application, business logic, and data access.[39]
- Three-tier software separates the presentation layer, business logic, and data access.[40]
- n-tier software adds additional layers for different servers to provide separate parts of the overall business logic, such as separate sales and inventory management servers.[41]
Key Terms
[edit | edit source]- CAD (Computer-Aided Design)
- The use of computer systems to assist in the creation, modification, analysis, or optimization of a design, particularly for manufacturing.[42]
- CAM (Computer-Aided Manufacturing)
- The use of computer software to control machine tools and related machinery in the manufacturing of workpieces.[43]
- EULA (End-User License Agreement)
- A legal contract entered into between a software developer or vendor and the user of the software, often where the software has been purchased by the user from an intermediary such as a retailer.[44]
- GPS (Global Positioning System)
- a satellite-based radio-navigation system owned by the United States government and operated by the United States Space Force.[45]
- MP3 (Moving Picture Experts Group Layer 3 Audio)
- An audio file format that uses a form of lossy data compression, accepted as the de facto standard of digital audio compression for the transfer and playback of music on most digital audio players.[46]
- MP4 (Moving Picture Experts Group Layer 4)
- A digital multimedia file format most commonly used to store video and audio, but can also be used to store other data such as subtitles and still images.[47]
- NDA (Non-Disclosure Agreement)
- A legal contract between at least two parties that outlines confidential material, knowledge, or information that the parties wish to share with one another for certain purposes, but wish to restrict access to.[48]
- SaaS (Software as a Service)
- A software licensing and delivery model in which software is licensed on a subscription basis and is centrally hosted.[49]
Assessments
[edit | edit source]See Also
[edit | edit source]References
[edit | edit source]- ↑ CompTIA: IT Fundamentals (ITF+) Exam Objectives FC0-U61
- ↑ Wikipedia: Productivity software
- ↑ Wikipedia: Word processor
- ↑ Wikipedia: Spreadsheet
- ↑ Wikipedia: Presentation program
- ↑ Wikipedia: Web browser
- ↑ Wikipedia: Vector graphics
- ↑ Wikipedia: Collaborative software
- ↑ Wikipedia: Email client
- ↑ Wikipedia: Web conferencing
- ↑ Wikipedia: Instant messaging
- ↑ Wikipedia: Workspace
- ↑ Wikipedia: Document collaboration
- ↑ Wikipedia: Business software
- ↑ Wikipedia: Databases
- ↑ Wikipedia: Project management software
- ↑ Wikipedia: Project
- ↑ Wikipedia: Vertical market software
- ↑ Wikipedia: Accounting software
- ↑ Wikipedia: Computing platform
- ↑ Wikipedia: Cross-platform software
- ↑ Wikipedia: Cross-platform software
- ↑ Wikipedia: Cross-platform software
- ↑ Wikipedia: Software license
- ↑ Wikipedia: Software license
- ↑ Wikipedia: Software license
- ↑ Wikipedia: Software license
- ↑ Wikipedia: Open-source license
- ↑ Proprietary software
- ↑ Wikipedia: Software license
- ↑ Wikipedia: Software license
- ↑ Wikipedia: Product key
- ↑ Wikipedia: Installation (computer programs)
- ↑ Wikipedia: Installation (computer programs)
- ↑ Wikipedia: Installation (computer programs)
- ↑ Wikipedia: Software as a service
- ↑ Wikipedia: Software architecture
- ↑ Wikipedia: Multitier architecture
- ↑ Wikipedia: Multitier architecture
- ↑ Wikipedia: Multitier architecture
- ↑ Wikipedia: Multitier architecture
- ↑ Wikipedia: Computer-aided design
- ↑ Wikipedia: Computer-aided manufacturing
- ↑ Wikipedia: End-user license agreement
- ↑ Wikipedia: Global Positioning System
- ↑ Wikipedia: MP3
- ↑ Wikipedia: MPEG-4 Part 14
- ↑ Wikipedia: Non-disclosure agreement
- ↑ Wikipedia: Software as a service
Database Concepts
[edit | edit source]This lesson introduces database concepts.
Objectives and Skills
[edit | edit source]Objectives and skills for the database fundamentals portion of IT Fundamentals certification include:[1]
- Explain database concepts and the purpose of a database.
- Usage of database
- Create
- Import/input
- Query
- Reports
- Flat file vs. database
- Multiple concurrent users
- Scalability
- Speed
- Variety of data
- Records
- Storage
- Data persistence
- Usage of database
- Compare and contrast various database structures.
- Structured vs. semi-structured vs. non-structured
- Relational databases
- Schema
- Tables
- Rows/records
- Fields/columns
- Primary key
- Foreign key
- Constraints
- Non-relational databases
- Key/value databases
- Document databases
Readings
[edit | edit source]Multimedia
[edit | edit source]- YouTube: Purpose of a Database
- YouTube: Various Database Structures
- YouTube: SQL vs NoSQL or MySQL vs MongoDB
- YouTube: Chapter 14 - IT Fundamentals+ (FC0-U61) Understanding Databases
Activities
[edit | edit source]- Research desktop databases. Include:
- hardware requirements
- operating system requirements
- maximum database size
- maximum number of concurrent users
- license (proprietary or open source)
- price
- market share
- Select a desktop database to use for the following activities. Download and install the database.
- LibreOffice Base is available free for anyone from LibreOffice.org. It requires a Java runtime environment (JRE), available free from java.com.
- Microsoft Access is available free for students through Microsoft: Azure for Education.
- Complete a tutorial for your selected desktop database.
- Use a desktop database.
- Using a text editor, copy the following list of names and scores and save it as a flat comma-separated values file named
scores.csv:Name,ScoreJoe Besser,70Curly Joe DeRita,0Larry Fine,80Curly Howard,65Moe Howard,100Shemp Howard,85 - Using your desktop database, import
scores.csv. - Open the imported table and view the results.
- Use a wizard to create a query for the imported table that displays the table in order by score from highest to lowest.
- Use a wizard to create a form for the imported table that allows you to view and modify names and scores.
- Use a wizard to create a report for the imported table using the query created above that displays the table in order by score from highest to lowest.
- Using a text editor, copy the following list of names and scores and save it as a flat comma-separated values file named
- Use relational and non-relational databases to compare and contrast what they do and how they work.
Lesson Summary
[edit | edit source]Database Concepts
[edit | edit source]





- A database is an organized collection of data.[2]
- A database is a collection of schemas, tables, queries, reports, views and other objects.[3]
- A query language is a computer language used to make queries (or questions about data) in databases and information systems.[4]
- A database server is a computer program that provides database services to other computer programs or computers as defined by the client–server model.[5]
- A database management system (DBMS) is a computer software application that interacts with the user, other applications, and the database itself to capture and analyze data. A general-purpose DBMS is designed to allow the definition, creation, querying, update, and administration of databases.[6]
- A database engine (or storage engine) is the underlying software component that a database management system (DBMS) uses to create, read, update and delete data from a database.[7]
Relational Databases
[edit | edit source]- A relational database presents data to the user as a collection of related tables with each table consisting of a set of rows and columns.[8]
- The schema of a database is its structure described in a formal language supported by the database management system (DBMS). The schema describes the tables, records (rows), fields (columns), and other database objects.[9]
- A database table is a collection of related data held in a structured format within a database consisting of fields (columns), and records (rows).[10]
- A database row or record represents a single, implicitly structured data item in a table.[11]
- A database column or field is a set of data values of a particular simple type, one value for each row of the database.[12]
- A primary key uniquely specifies a record within a table. In order for an attribute to be a good primary key it must not repeat.[13]
- A foreign key is a field in a relational table that matches the primary key column of another table. The foreign key can be used to cross-reference tables. Foreign keys do not need to have unique values in the referencing relation. [14]
- A database constraint restricts the data that can be stored in relations. The two principal rules for the relational model are known as entity integrity and referential integrity.[15]
Non-Relational Databases
[edit | edit source]- Semi-structured data does not obey the formal structure of data models associated with relational databases or other forms of data tables. Instead, tags are used to separate data elements indicating records and fields. Examples include XML and JSON.[16]
- A NoSQL (originally referring to "non SQL" or "non relational") database provides a mechanism for storage and retrieval of data that is modeled in means other than the tabular relations used in relational databases.[17]
- NoSQL database benefits include simplicity and scalability, but lack enforced consistency across the data.[18]
- NoSQL data structures include key-value pairs and document databases.[19]
Database Storage
[edit | edit source]- Database tables and indexes may be stored on disk in one of a number of forms, including ordered/unordered flat files and a variety of structured binary files.[20]
- Unordered files offer good insertion performance but inefficient retrieval times. Ordered files provide more efficient retrieval but lower insertion efficiency.[21]
- A database index is a data structure that improves the speed of data retrieval operations on a database table. Indexes are used to quickly locate data without searching every row in a database table every time a database table is accessed.[22]
- A hierarchical database is a data model in which the data is organized into a tree-like structure. This model mandates that each child record has only one parent, whereas each parent record can have one or more child records.[23]
- A flat-file database is a database which is stored on its host computer system as an ordinary file.[24]
- File-based database engines have limited performance compared to process-based database engines in regard to:[25]
- Multiple concurrent users
- Scalability
- Speed
- Variety of data
- Databases may employ storage redundancy through replication (with one or more copies) to increase data availability (both to improve performance of simultaneous multiple end-user accesses to a database object, and to provide resiliency in a case of partial failure of a database).[26]
Database Usage
[edit | edit source]- Desktop database applications often support different user interface options such as:[27]
- Tables to hold or access stored data
- Queries to select and modify table data for forms and reports
- Forms to display and modify data on screen
- Reports to display data on paper or in digital documents.
- Desktop database applications often support import and export of a wide variety of data file formats.[28]
Key Terms
[edit | edit source]- export
- The automated or semi-automated output of data sets between different software applications.[29]
- field
- Each column in a table represents a set of data values of a particular simple type, one value for each row of the database.[30]
- import
- The automated or semi-automated input of data sets between different software applications.[31]
- record
- Each row in a table represents a set of related data, and every row in the table has the same structure.[32]
- scalability
- The property of a system to handle a growing amount of work by adding resources to the system.[33]
- schema
- The structure of a database described in a formal language supported by the database management system (DBMS).[34]
Assessments
[edit | edit source]- Flashcards: Quizlet: IT Fundamentals - Database Concepts
- Quiz: Quizlet: IT Fundamentals - Database Concepts
See Also
[edit | edit source]References
[edit | edit source]- ↑ CompTIA: IT Fundamentals (ITF+) Exam Objectives FC0-U61
- ↑ Wikipedia:Database
- ↑ Wikipedia:Database
- ↑ Wikipedia:Query language
- ↑ Wikipedia:Database server
- ↑ Wikipedia:Database
- ↑ Wikipedia: Database engine
- ↑ Wikipedia: Relational database
- ↑ Wikipedia: Database schema
- ↑ Wikipedia:Table (database)
- ↑ Wikipedia: Row (database)
- ↑ Wikipedia: Column (database)
- ↑ Wikipedia:Relational Database
- ↑ Wikipedia:Relational Database
- ↑ Wikipedia:Relational database model
- ↑ Wikipedia: Semi-structured data
- ↑ Wikipedia: NoSQL
- ↑ Wikipedia: NoSQL
- ↑ Wikipedia: NoSQL
- ↑ Wikipedia: Database storage structures
- ↑ Wikipedia: Database storage structures
- ↑ Wikipedia:Database index
- ↑ Wikipedia:Hierarchical database model
- ↑ Wikipedia:Flat file database
- ↑ Wikipedia: Database engine
- ↑ Wikipedia: Database
- ↑ Go Free: LibreOffice Base Tutorial
- ↑ Go Free: LibreOffice Base Tutorial
- ↑ Wikipedia: Import and export of data
- ↑ Wikipedia: Column (database)
- ↑ Wikipedia: Import and export of data
- ↑ Wikipedia: Row (database)
- ↑ Wikipedia: Scalability
- ↑ Wikipedia: Database schema
Database Use
[edit | edit source]This lesson introduces database use.
Objectives and Skills
[edit | edit source]Objectives and skills for the database use portion of IT Fundamentals certification include:[1]
- Summarize methods used to interface with databases.
- Relational methods
- Data manipulation
- Select
- Insert
- Delete
- Update
- Data definition
- Create
- Alter
- Drop
- Permissions
- Data manipulation
- Database access methods
- Direct/manual access
- Programmatic access
- User interface/utility access
- Query/report builders
- Export/import
- Database dump
- Backup
- Relational methods
Readings
[edit | edit source]Multimedia
[edit | edit source]Activities
[edit | edit source]- Complete one or more of the following tutorials:
- Practice writing single-table SELECT statements using W3Schools SQL TryIt Editor.
- Select all customers (SELECT *).
- Select only customer id and customer name fields (SELECT fields).
- Select customer name, address, city, and postal code for all customers from the United Kingdom (WHERE field = 'value').
- Select contact name and customer name for all customers, sorted alphabetically by contact name (ORDER BY field).
- Count the total number of customers (COUNT(*)).
- Count the number of customers from each country (GROUP BY).
- Count the number of customers from each country and sort the list in descending order by count and ascending order by country in case of a tie (GROUP BY, ORDER BY).
- Count the number of customers from each country and sort the list in descending order by count and ascending order by country in case of a tie, listing only those countries with more than 10 customers (GROUP BY, HAVING, ORDER BY).
- Practice writing multiple-table SELECT statements using W3Schools SQL TryIt Editor.
- Select customer name, order ID, and order date for all customers (INNER JOIN).
- Select customer name, order number, and order date for all customers, renaming the OrderID field as Order Number (INNER JOIN, AS).
- Select customer name, order number, and order date for all customers, sorted by customer name and order number (INNER JOIN, AS, ORDER BY).
- Select order number, order date, product name, and quantity ordered for all customers (INNER JOIN, AS).
- Select order number, order date, product name, quantity ordered, and extended price (quantity * price) for all customers (INNER JOIN, AS, calculated field).
- Select order number, order date, product name, quantity ordered, and extended price for customer 2 (INNER JOIN, AS, calculated field, WHERE).
- Select order number, order date, product name, quantity ordered, and extended price for customer 'Around the Horn' (INNER JOIN, AS, calculated field, WHERE).
- Practice writing INSERT, UPDATE, and DELETE statements using W3Schools SQL TryIt Editor.
- Add a new shipper with ID 4, name 'On Time Delivery', and phone '(503) 555 0123' (INSERT).
- Increase prices on all products by 1 (UPDATE).
- Reduce prices on all products by 1 (UPDATE).
- Change the new shipper's name from 'On Time Delivery' to 'On-Time Delivery' (UPDATE, WHERE).
- Delete the new shipper (DELETE, WHERE).
- Research SQL statements.
- Research CREATE, ALTER, and DROP. Note how they differ from INSERT, UPDATE, and DELETE.
- Research GRANT and REVOKE. Note how they may be applied broadly to tables and queries (views) or specifically to individual fields in a table or query (view).
Lesson Summary
[edit | edit source]Relational Databases
[edit | edit source]







- A relational database is a digital database where all data is represented in terms of tuples (rows or records), grouped into relations (tables).[2]
- Each row in a table has its own unique key.[3]
- A primary key is a specific choice of a minimal set of attributes (columns) that uniquely specify a tuple (row) in a relation (table).[4]
- A foreign key is a set of attributes (columns) whose values exist in another relation (table), and uniquely identify a tuple (row) in the other table[5]
- Constraints make it possible to restrict the domain (possible values) of an attribute (column). Constraint options include:[6]
- Primary key
- Foreign key
- Stored procedure (data validation)
- Index
- Most relational databases use the SQL data definition and query language.[7]
Data Definition Language
[edit | edit source]- Data Definition Language (DDL) is a syntax similar to a computer programming language for defining data structures, especially database schemas.[8]
- A database schema is its structure described in a formal language supported by the database management system (DBMS).[9]
- DDL statements create and modify database objects such as tables, indexes, and users.[10]
- Common DDL statements are CREATE, ALTER, and DROP.[11]
- The
CREATEcommand is used to establish a new database, table, index, or stored procedure.[12] - The
ALTERstatement modifies an existing database object.[13] - The
DROPstatement destroys an existing database, table, index, or view.[14]
Data Query Language
[edit | edit source]- Data Query Language (DQL) is used for performing queries on the data within schema objects.[15]
- The
SELECTstatement returns a result set of records from one or more tables.[16] - The
SELECTstatement is often considered part of Data Manipulation Language (DML) rather than a separate subset.[17] - The basic
SELECTstatement syntax isSELECT <column> [AS <alias>, ...] FROM <table> [AS <alias>, ...].[18][19] - An asterisk ("*") can be used to specify that the query should return all columns of the queried tables.[20]
- A
WHEREclause in SQL specifies that a SQL Data Manipulation Language (DML) statement should only affect rows that meet specified criteria.[21] - The basic
WHEREclause syntax is<SQL-DML-Statement> FROM <table> WHERE <predicate>.[22] - By default, relational database systems may return data rows in any order, or more specifically, without any order.[23]
- An
ORDER BYclause in SQL specifies that a SQL SELECT statement returns a result set with the rows being sorted by the values of one or more columns.[24] - The basic
ORDER BYclause syntax isSELECT <column(s)> FROM <table(s)> ORDER BY <column> [DESC] [NULLS FIRST], ....[25] - The
DESCkeyword will sort a given column in descending order.[26] - A
JOINclause combines columns from one or more tables in a relational database.[27]
Data Manipulation Language
[edit | edit source]- Data Manipulation Language (DML) is a computer programming language used for adding (inserting), deleting, and modifying (updating) data in a database.[28]
- The
INSERTstatement adds one or more records to any single table in a relational database.[29] - The basic
INSERTsyntax isINSERT INTO <table>(<column(s)>) VALUES(<value(s)>)[30] - The
UPDATEstatement changes the data of one or more records in a table. Either all the rows can be updated, or a subset may be chosen using a condition.[31] - The basic
UPDATEsyntax isUPDATE <table> SET <column> = <value>, ... [WHERE <condition>][32] - The
DELETEstatement removes one or more records from a table. A subset may be defined for deletion using a condition, otherwise all records are removed.[33] - The basic
DELETEsyntax isDELETE FROM <table> [WHERE <condition>][34]
Data Control Language
[edit | edit source]- Data Control Language (DCL) is a syntax similar to a computer programming language used to control access (authorization) to data stored in a database.[35]
GRANTallows specified users to perform specified tasks.[36]REVOKEremoves user accessibility to a database object.[37]- The operations for which privileges may be granted to or revoked from a user or role apply to both Data Definition Language (DDL) and Data Manipulation Language (DML).[38]
Database Access Methods
[edit | edit source]- The functionality provided by a DBMS can vary greatly, and often include:[39]
- Data storage, retrieval and update
- User accessible catalog or data dictionary describing the metadata
- Support for transactions and concurrency
- Facilities for recovering the database should it become damaged
- Support for authorization of access and update of data
- Access support from remote locations
- Enforcing constraints to ensure data in the database abides by certain rules
- It is generally expected the DBMS will provide a set of command line or graphical utilities for direct access to the database for administration.[40]
- A programmer will code interactions to the database (sometimes referred to as a datasource) via an application program interface (API) or via a database language.[41]
- External interaction with the database will be via an application program that can range from a database tool that allows users to execute SQL queries textually or graphically to a web site that uses a database to store and search information.[42]
- Query and reporting applications often support different user interface options such as:[43]
- Tables to hold or access stored data
- Queries to select and modify table data for forms and reports
- Forms to display and modify data on screen
- Reports to display data on paper or in digital documents.
Export/Import
[edit | edit source]- A comma-separated values (CSV) file is a delimited text file that uses a comma to separate values. Each line of the file is a data record. Each record consists of one or more fields, separated by commas. The use of the comma as a field separator is the source of the name for this file format.[44]
- A CSV file typically stores tabular data (numbers and text) in plain text, in which case each line will have the same number of fields. CSV files may be used to export data from and import data to a database.[45]
- A database backup operation is performed occasionally or continuously in case it becomes necessary to restore a database back to a previous state.[46]
- A database dump contains a record of the table structure and/or the data from a database and is usually in the form of a list of SQL statements. A database dump is most often used for backing up a database so that its contents can be restored in the event of data loss.[47]
Key Terms
[edit | edit source]- CRUD (Create, Read, Update, Delete)
- The four basic functions of persistent storage.[48]
- DDL (Data Definition Language)
- A syntax similar to a computer programming language for defining data structures, such as tables and indexes.[49]
- DML (Data Manipulation Language)
- A computer programming language used for adding (inserting), deleting, and modifying (updating) data in a database.[50]
- RDBMS (Relational Database Management System)
- A software system used to maintain relational databases.[51]
- SQL (Structured Query Language)
- A domain-specific language used in programming and designed for managing data held in a relational database management system (RDBMS).[52]
Assessments
[edit | edit source]See Also
[edit | edit source]References
[edit | edit source]- ↑ CompTIA: IT Fundamentals (ITF+) Exam Objectives FC0-U61
- ↑ Wikipedia: Relational model
- ↑ Wikipedia: Relational database
- ↑ Wikipedia: Primary key
- ↑ Wikipedia: Foreign key
- ↑ Wikipedia: Relational database
- ↑ Wikipedia: Relational model
- ↑ Wikipedia: Data definition language
- ↑ Wikipedia: Database schema
- ↑ Wikipedia: Data definition language
- ↑ Wikipedia: Data definition language
- ↑ Wikipedia: Data definition language
- ↑ Wikipedia: Data definition language
- ↑ Wikipedia: Data definition language
- ↑ Wikipedia: Data query language
- ↑ Wikipedia: Select (SQL)
- ↑ Wikipedia: Data query language
- ↑ Wikipedia: SQL
- ↑ Wikipedia: Select (SQL)
- ↑ Wikipedia: SQL
- ↑ Wikipedia: Where (SQL)
- ↑ Wikipedia: Where (SQL)
- ↑ Wikipedia: Order by
- ↑ Wikipedia: Order by
- ↑ Wikipedia: Order by
- ↑ Wikipedia: Order by
- ↑ Wikipedia: Join (SQL)
- ↑ Wikipedia: Data manipulation language
- ↑ Wikipedia: Insert (SQL)
- ↑ Wikipedia: Insert (SQL)
- ↑ Wikipedia: Update (SQL)
- ↑ Wikipedia: Update (SQL)
- ↑ Wikipedia: Delete (SQL)
- ↑ Wikipedia: Delete (SQL)
- ↑ Wikipedia: Data control language
- ↑ Wikipedia: Data control language
- ↑ Wikipedia: Data control language
- ↑ Wikipedia: Data control language
- ↑ Wikipedia: Database
- ↑ Wikipedia: Database
- ↑ Wikipedia: Database
- ↑ Wikipedia: Database
- ↑ Go Free: LibreOffice Base Tutorial
- ↑ Wikipedia: Comma-separated files
- ↑ Wikipedia: Comma-separated files
- ↑ Wikipedia: Database
- ↑ Wikipedia: Database dump
- ↑ Wikipedia: Create, read, update and delete
- ↑ Wikipedia: Data definition language
- ↑ Wikipedia: Data manipulation language
- ↑ Wikipedia: Relational database
- ↑ Wikipedia: SQL
Networking
[edit | edit source]




This lesson introduces basic networking concepts.
Objectives and Skills
[edit | edit source]Objectives and skills for the networking portion of IT Fundamentals certification include:[1]
- Explain basic networking concepts.
- Basics of network communication
- Device addresses
- IP address
- MAC address
- Devices
- Modem
- Router
- Switch
- Access point
- Firewall
- Given a scenario, install, configure and secure a basic wireless network.
- 802.11a/b/g/n/ac
- Older vs. newer standards
- Speed limitations
- Interference and attenuation factors
- Best practices
- Change SSID
- Change default password
- Encrypted vs. unencrypted
- Open
- Captive portal
- WEP
- WPA
- WPA2
- 802.11a/b/g/n/ac
Readings
[edit | edit source]Multimedia
[edit | edit source]- YouTube: Basic Networking Concepts
- YouTube: Install, Configure & Secure a Basic Wireless Network
- YouTube: Chapter 10 - IT Fundamentals+ (FC0-U61) Configuring Network and Internet Connectivity
Activities
[edit | edit source]- Check IP address settings for your local network:
- Windows:
- Review Microsoft: How do I fix network adapter problems? and Microsoft: Change TCP/IP Settings. Review network settings for your system.
- Review ipconfig. Complete the activities to display IP address information, all information, and release and renew a dynamic IP address.
- macOS:
- Review Apple: About Network Utility. Use Network Utility to review network settings for your system.
- Review MacWorld: Configuring Your Mac's Network Settings Use System Preferences / Network to review network settings for your system. Use the Advanced button and TCP/IP settings to renew your DHCP lease.
- Review Wikipedia: ifconfig. Use
ifconfigto review network settings for your system.
- Linux:
- Review YoLinux: Network GUI Configuration Tools. Use Network Configuration or System Settings / Networking to review network settings for your system.
- Review Wikipedia: ifconfig. Use
ifconfigto review network settings for your system. Review CyberCiti: Linux Force DHCP Client to Renew IP Address. Usedhclientto release and renew a dynamic IP address.
- Windows:
- Research network devices. Compare each of the following. Include device purpose, price range for small-office/home-office devices, and the top vendor(s) by market share for each.
- Modem
- Router
- Switch
- Access point
- Firewall
- Set up and configure a basic wireless router using either a router emulator or your home router:
- Use a Cisco: Small Business Router Emulator to set up and configure a basic wireless router. (Note: The emulator will not save configuration changes.):
- Change the default administrator password for the device.
- Configure wireless security by setting a new SSID name and setting the security mode to WPA2 with a strong password.
- Research current firmware releases for the device. Locate the router's firmware upgrade page and review instructions from the router's Help page on how to update the firmware.
- Review settings for your home router:
- Verify that the administrator password has been changed from the default.
- Verify that the SSID security mode is set to WPA2 with a strong password.
- Research current firmware releases for the device and determine whether a firmware update is required.
- Use a Cisco: Small Business Router Emulator to set up and configure a basic wireless router. (Note: The emulator will not save configuration changes.):
- Review Wikipedia: Wardriving. Use a free wireless scanner and scan your environment for wireless networks:
- Windows:
- Review Archive: BitDreamers: Improve WLAN Signal Without Additional Tools on Windows.and Wikipedia: NetSpot.
- Use the
netsh wlan show networks mode=bssidcommand or download and install NetSpot and scan for wireless networks.
- macOS:
- Review AppStorm: How to Discover Any Network with iStumbler and Wikipedia: NetSpot.
- Download and install iStumbler or NetSpot and scan for wireless networks
- Linux:
- Review TuxMobil.org: Linux Wireless Sniffer.
- Download and install a wireless scanner and scan for wireless networks.
- Android:
- Review Google: farproc Wifi Analyzer.
- Download and install Wifi Analyzer and scan for wireless networks.
- iOS:
- Review WLANBook: Free WiFi Scanner for iPhone and iPad Without Jailbreak.
- Download and install the Apple AirPort Utility and scan for wireless networks.
- Windows:
- Share a folder and connect to the shared folder:
- Windows GUI:
- Review Microsoft: File Sharing Essentials. Share a folder on your system.
- From another computer, use a UNC path to connect to the shared folder.
- Windows CLI:
- Review Microsoft: Net Share. Use the
net sharecommand to share a folder on your system. - Review Microsoft: Net Use. From another computer, use the
net usecommand to connect to the shared folder.
- Review Microsoft: Net Share. Use the
- macOS:
- Review Apple: Set up file sharing on Mac. Share a folder on your system.
- Review Apple: Connect to Shared Computers and File Servers on a Network. From another computer, connect to the shared folder.
- Linux:
- Review TechGage: Using Samba to Share Your Linux Folders. Install Samba if necessary and share a folder on your system.
- Review HowToGeek: 3 Easy Ways to Connect to Windows Shared Folders from Linux. From another computer, connect to the shared folder.
- Windows GUI:
Lesson Summary
[edit | edit source]Networking Concepts
[edit | edit source]- A computer network or data network is a telecommunications network that allows computers to exchange data. Networked computing devices pass data to each other in the form of packets across connections established using either cable or wireless media.[2]
- A network packet is a formatted unit of data sent through a network to the destination. Once packets arrive, they are reassembled into their original message.[3]
- Wired media includes coaxial cable, twisted-pair cable, and optical fiber.[4]
- Wireless local area network connections use spread spectrum technology based on a common flavor of open-standards wireless radio-wave technology defined as IEEE 802.11 and known as Wi-Fi.[5]
- A network interface controller (NIC) is hardware that provides a computer with the ability to access the transmission media, and has the ability to process low-level network information.[6]
Device Addresses
[edit | edit source]- In Ethernet networks, each NIC has a unique 48-bit Media Access Control (MAC) address.[7]
- An Internet Protocol address (IP address) is a numerical label assigned to each device participating in a network that uses the Internet Protocol for communication. An IP address serves two principal functions: host identification and network addressing.[8]
- IP addresses are 32-bit (IPv4) or 128-bit (IPv6) numbers usually written and displayed in human-readable notations, such as 198.51.100.1 (IPv4), and 2001:db8:0:1234:0:567:8:1 (IPv6).[9]
- IP addresses are assigned to a host either anew at the time of booting, or permanently by fixed configuration of its hardware or software. Persistent configuration is also known as using a static IP address. In contrast, in situations when the computer's IP address is assigned newly each time, this is known as using a dynamic IP address.[10]
- Static IP addresses are manually assigned to a computer by an administrator.[11]
- Dynamic IP addresses are assigned either by the computer interface or host software itself through automatic configuration, or assigned by a server using Dynamic Host Configuration Protocol (DHCP).[12]
Device Types
[edit | edit source]- A switch is a device that connects and filters multiple network segments or devices, by forwarding data only to one or multiple devices that need to receive the data based on destination MAC address.[13]
- A router is a device that forwards data packets between different computer networks based on network address (IP address).[14]
- A modem is a device used to connect network nodes via wire not originally designed for digital network traffic, by modulating the digital signal to produce an analog signal for transmission.[15]
- A firewall is a device used to control network security and access rules by rejecting access requests from unrecognized sources while allowing actions from recognized ones.[16]
- An access point is a device that allows wireless devices to connect to a wired network using Wi-Fi, or related standards.[17]
Wireless Networking
[edit | edit source]- Wi-Fi is a family of wireless networking technologies, based on the IEEE 802.11 family of standards.[18]
- Historically, wireless equipment has simply listed versions of Wi-Fi using the name of the IEEE standard that it supports. In 2018, the Wi-Fi alliance standardized generational numbering.[19]
- Wi-Fi generations (IEEE standards) and maximum connection speeds include:[20]
- Wi-Fi 1 (802.11b) - 11 Mbps
- Wi-Fi 2 (802.11a) - 54 Mbps
- Wi-Fi 3 (802.11g) - 54 Mbps
- Wi-Fi 4 (802.11n) - 600 Mbps
- Wi-Fi 5 (802.11ac) - 6,933 Mbps
- Wi-Fi 6 (802.11ax) - 9,608 Mbps
- 802.11b/g/n can use the 2.4 GHz ISM band. In this frequency band equipment may occasionally suffer interference from microwave ovens, cordless telephones, USB 3.0 hubs, and Bluetooth devices.
- Attenuation is an important consideration in wireless telecommunication. Attenuation limits the range of radio signals and is affected by the materials a signal must travel through (e.g., air, wood, concrete, rain).[21]
- The SSID (service set identifier) is the wireless network name.[22]
- Anyone within the geographical network range of an open, unencrypted wireless network can "sniff", or capture and record, the traffic, gain unauthorized access to internal network resources as well as to the internet, and then use the information and resources to perform disruptive or illegal acts.[23]
- Wi-Fi encryption options include WEP, WPA, and WPA2.[24]
- WEP is a notoriously weak security standard. The password it uses can often be cracked in a few minutes with a basic laptop computer and widely available software tools.
- WPA was a quick alternative to improve security over WEP.
- The current standard is WPA2.
- A captive portal is a web page accessed with a web browser that is displayed to newly connected users of a Wi-Fi or wired network before they are granted broader access to network resources.[25]
- Best practice is to change the default network SSID and password, and use WPA2 encryption.[26]
Key Terms
[edit | edit source]- AES (Advanced Encryption Standard)
- A widely accepted data encryption standard using symmetric cryptography and supporting key lengths of 128, 192 and 256 bits which supersedes DES.[27]
- APIPA (Automatic Private Internet Protocol Addressing)
- A random link-local address starting with 169.254.x.y used when a device fails to obtain an address through DHCP.[28]
- ARP (Address Resolution Protocol)
- A communication protocol used for discovering the link layer address, such as a MAC address, associated with a given internet layer address, typically an IPv4 address.[29]
- DHCP (Dynamic Host Configuration Protocol)
- A standardized network protocol used on Internet Protocol (IP) networks for dynamically distributing network configuration parameters, such as IP addresses for interfaces and services.[30]
- DNS (Domain Name Service or Domain Name Server)
- A hierarchical distributed naming system for computers, services, or any resource connected to the Internet or a private network.[31]
- ICMP (Internet Control Message Protocol)
- A supporting protocol in the Internet protocol suite used to send error messages and operational information indicating success or failure when communicating with another IP address.[32]
- LAN (Local Area Network)
- A computer network that interconnects computers within a limited geographic area such as a home, school, computer laboratory, or office building.[33]
- MAC (Media Access Control)
- The layer that controls the hardware responsible for interaction with the wired, optical or wireless network transmission medium.[34]
- POTS (Plain Old Telephone Service)
- Voice-grade telephone service employing analog signal transmission over copper loops.[35]
- PXE (Preboot Execution Environment)
- A standardized client-server environment that boots a device from software retrieved from the network rather than a local secondary device.[36]
- SMB (Server Message Block)
- A network communication protocol for providing shared access to files, printers, and serial ports between nodes on a network.[37]
- SOHO (Small Office, Home Office)
- The category of business or cottage industry that typically involves from 1 to 10 workers.[38]
- SSID (Service Set Identifier)
- A unique identifier for a wireless LAN.[39]
- TKIP (Temporal Key Integrity Protocol)
- A stopgap security protocol used in the IEEE 802.11 wireless networking standard, and used to replace WEP without requiring the replacement of legacy hardware. TKIP is no longer considered secure.[40]
- WAN (Wide Area Network)
- A network that covers a broad geographic area using leased telecommunication lines.[41]
- WAP (Wireless Access Point)
- A networking hardware device that allows other Wi-Fi devices to connect to a wired network.[42]
- WEP (Wired Equivalency Privacy)
- The original security algorithm for IEEE 802.11 wireless networks, and superseded by WPA. WEP is no longer considered secure.[43]
- Wi-Fi (Wireless Fidelity)
- A local area wireless technology that allows an electronic device to participate in computer networking using 2.4 GHz and 5 GHz bands.[44]
- WLAN (Wireless Local Area Network)
- A wireless computer network that links two or more devices using a wireless distribution method within a limited area such as a home, school, computer laboratory, or office building.[45]
- WPA (Wireless Protected Access)
- A wireless computer network security protocol based on TKIP.[46]
- WPA2 (Wireless Protected Access 2)
- A wireless computer network security protocol based on AES.[47]
Assessments
[edit | edit source]- Flashcards: Quizlet: IT Fundamentals - Networking
- Quiz: Quizlet: IT Fundamentals - Networking
See Also
[edit | edit source]References
[edit | edit source]- ↑ CompTIA: IT Fundamentals (ITF+) Exam Objectives FC0-U61
- ↑ Wikipedia: Computer network
- ↑ Wikipedia: Computer network
- ↑ Wikipedia: Computer network
- ↑ Wikipedia: Computer network
- ↑ Wikipedia: Computer network
- ↑ Wikipedia: Computer network
- ↑ Wikipedia: IP address
- ↑ Wikipedia: IP address
- ↑ Wikipedia: IP address
- ↑ Wikipedia: IP address
- ↑ Wikipedia: IP address
- ↑ Wikipedia: Computer network
- ↑ Wikipedia: Computer network
- ↑ Wikipedia: Computer network
- ↑ Wikipedia: Computer network
- ↑ Wikipedia: Wireless access point
- ↑ Wikipedia: Wi-Fi
- ↑ Wikipedia: Wi-Fi
- ↑ Wikipedia: Wi-Fi
- ↑ Wikipedia: Attenuation
- ↑ Wikipedia: Service set (802.11 network)
- ↑ Wikipedia: Wireless security
- ↑ Wikipedia: Wireless security
- ↑ Wikipedia: Captive portal
- ↑ CompTIA: IT Fundamentals (ITF+) Exam Objectives FC0-U61
- ↑ Wikipedia: Advanced Encryption Standard
- ↑ Wikipedia: Link-local address
- ↑ Wikipedia: Address Resolution Protocol
- ↑ Wikipedia: Dynamic Host Configuration Protocol
- ↑ Wikipedia: Domain Name System
- ↑ Wikipedia: Internet Control Message Protocol
- ↑ Wikipedia: Local area network
- ↑ Wikipedia: Medium access control
- ↑ Wikipedia: Plain old telephone service
- ↑ Wikipedia: Preboot Execution Environment
- ↑ Wikipedia: Server Message Block
- ↑ Wikipedia: Small office/home office
- ↑ Wikipedia: Service set (802.11 network)
- ↑ Wikipedia: Temporal Key Integrity Protocol
- ↑ Wikipedia: Wide area network
- ↑ Wikipedia: Wireless access point
- ↑ Wikipedia: Wired Equivalent Privacy
- ↑ Wikipedia: Wi-Fi
- ↑ Wikipedia: Wireless LAN
- ↑ Wikipedia: Wi-Fi Protected Access
- ↑ Wikipedia: Wi-Fi Protected Access
Internet
[edit | edit source]
This lesson introduces Internet services and web browsers.
Objectives and Skills
[edit | edit source]Objectives and skills for the Internet portion of IT Fundamentals certification include:[1]
- Compare and contrast common Internet service types.
- Fiber optic
- Cable
- DSL
- Wireless
- Radio frequency
- Satellite
- Cellular
- Given a scenario, configure and use web browsers.
- Caching/clearing cache
- Deactivate client-side scripting
- Browser add-ons/extensions
- Add
- Remove
- Enable/disable
- Private browsing
- Proxy settings
- Certificates
- Valid
- Invalid
- Popup blockers
- Script blockers
- Compatible browser for application(s)
- Explain basic networking concepts.
- Basics of network communication
- Basics of packet transmission
- DNS
- URL-to-IP translation
- LAN vs. WAN
- Basic protocols
- HTTP/S
- POP3
- IMAP
- SMTP
- Basics of network communication
Readings
[edit | edit source]- Wikipedia: Internet access
- Wikipedia: Web browser
- Wikipedia: Internet protocol suite
- Wikipedia: Domain Name System
Multimedia
[edit | edit source]Activities
[edit | edit source]
- Research plans available from different wired (fiber optic, cable, DSL) and wireless (radio frequency, satellite, cellular) Internet providers. Compare mobility, availability, bandwidth, reliability, delay, concurrent connections, security, and cost. How is speed measured for these services (bps, Kbps, Mbps, Gbps, or Tbps)?
- Research email protocols. Identify the differences between HTTPS, POP3, IMAP, and SMTP. Note what each protocol does and when each should be used. Check settings in your preferred email program to determine which email protocols you are using.
- Complete the GCF Global: Internet Safety tutorials.
- Configure and use web browsers. Try two or three different web browsers (Chrome, Firefox, Edge, Safari, etc.) for each of the following activities.
- View cache contents and then clear the cache.
- Disable JavaScript and test website functionality. Reenable JavaScript when you finish testing.
- Check installed browser extensions (add-ons). Install Privacy Badger to experiment with if you don't currently have any extensions installed. Practice enabling and disabling extensions. Remove any extensions you don't recall installing or don't use anymore.
- Test private browsing. Research what actual privacy private browsing provides and what privacy it doesn't or can't address.
- View and test web site certificates.
- Review GlobalSign: How to View SSL Certificate Details in Each Browser and What You Can Learn. Compare SSL certificates for the GlobalSign page and this Wikiversity page.
- Visit BadSSL.com and test your browser's response to different certificate errors.
- Use a protocol analyzer to view the basics of packet transmission and URL-to-IP translation:
- Review Wireshark and the lessons on how to:
- Install Wireshark
- Start a Wireshark Capture
- Stop a Wireshark Capture
- Capture Network Traffic
- Filter Displayed Traffic
- Start a Wireshark capture and then use a browser to navigate to a website you haven't visited recently (within the last day or so).
- Stop the Wireshark capture.
- Filter for DNS traffic and observe how the DNS protocol was used to translate the URL's fully-qualified domain name (FQDN) into an IP address.
- Review Wireshark and the lessons on how to:
- Use a protocol analyzer to compare HTTP and HTTPS traffic:
- Start a Wireshark capture and then use a browser to navigate to a website using HTTP, and another website using HTTPS.
- Stop the Wireshark capture.
- Filter for HTTP traffic and observe that the contents of the traffic are visible in the capture.
- Filter for HTTPS traffic and observe that the contents of the traffic are encrypted and not visible in the capture.
Lesson Summary
[edit | edit source]Internet Service
[edit | edit source]









- An Internet service provider (ISP) is an organization that provides services for accessing, using, or participating in the Internet.[2]
- Wired Internet access options include analog and digital computer modems attached to telephone lines, coaxial television cable (CATV), and fiber optic cables.[3]
- Wireless Internet access options include Wi-Fi, cellular, and satellite connections.[4]
- Optical fiber is a flexible, transparent fiber used most often as a means to transmit light between the two ends of the fiber and permit transmission over longer distances and at higher bandwidths (data transfer rates) than electrical cables.[5]
- Cable Internet is a form of broadband Internet access which uses the same coaxial cable infrastructure as cable television.[6]
- Digital subscriber line (DSL) is a family of technologies that are used to transmit digital data over telephone lines.[7]
- Wireless communication is the electromagnetic transfer of information between two or more points that are not connected by an electrical conductor.[8]
- The frequencies of the radio spectrum that are available for use for communication are treated as a public resource and are regulated by government organizations. These regulations determine which frequency ranges can be used for what purpose and by whom.[9]
- Wi-Fi technology may be used to provide local network and Internet access to devices that are within range of one or more routers that are connected to the Internet.[10]
- The Wi-Fi coverage of one or more interconnected access points (hotspots) can extend from an area as small as a few rooms to as large as many square kilometers.[11]
- Satellite Internet access is Internet access provided through communications satellites.[12]
- Mobile Internet refers to access to the internet via a cellular telephone service provider.[13]
Web Browsers
[edit | edit source]- A web browser (commonly referred to as a browser) is a software application for retrieving, presenting and traversing information resources on the World Wide Web.[14]
- The primary purpose of a web browser is to bring information resources to the user, allowing them to view the information, and then access other linked information.[15]
- A browser cache is used for temporary storage of web documents, such as HTML pages and images, to reduce bandwidth usage, server load, and perceived lag.[16]
- Client-side scripting, typically using JavaScript, changes interface behaviors within a specific web page in response to mouse or keyboard actions, or at specified timing events.[17]
- A browser extension is a plug-in that extends the functionality of a web browser.[18]
- Browser extensions are used for improving a browser's user interface, security or accessibility, blocking advertisements, and various other features to make browsing the internet easier and more pleasant.[19]
- Browser extensions have access to everything done by the browser, and can do things like inject ads into web pages, or make "background" HTTP requests to third-party servers. As a result, a malicious browser extension may take action against the interest of the user that installed it.[20]
- Private browsing is a feature in some web browsers where the browser creates a temporary session that is isolated from the browser's main session and user data. Browsing history is not saved, and local data associated with the session, such as cookies, are cleared when the session is closed. These modes are designed primarily to prevent data and history associated with a particular browsing session from persisting on the device, or being discovered by another user of the same device. Private browsing modes do not necessarily protect users from being tracked by other websites or their Internet service provider (ISP).[21]
- A proxy server is a server application or appliance that acts as an intermediary for requests from clients seeking resources from servers that provide those resources.[22]
- A public key certificate, also known as a digital certificate or identity certificate, is an electronic document used to prove the ownership of a public key. The certificate includes information about the key, information about the identity of its owner (called the subject), and the digital signature of an entity that has verified the certificate's contents (called the issuer). If the signature is valid, and the software examining the certificate trusts the issuer, then it can use that key to communicate securely with the certificate's subject.[23]
- Web development and design technologies allow an author to associate any item on a pop-up with any action, including with a cancel or innocent looking button. All major web browsers let users block unwanted pop-ups almost completely.[24]
- Script blockers block active (executable) web content, which a user can wholly or partially unblock by whitelisting a site or domain from the browser or browser extension's toolbar menu.[25]
- Cross-browser compatibility is the ability of a website or web application to function across different browsers and degrade gracefully when browser features are absent or lacking.[26]
Networking Concepts
[edit | edit source]- The Internet protocol suite provides end-to-end data communication specifying how data should be packetized, addressed, transmitted, routed, and received. This functionality is organized into four abstraction layers, which classify all related protocols according to the scope of networking involved. From lowest to highest, the layers are the link layer, containing communication methods for data that remains within a single network segment (link); the internet layer, providing internetworking between independent networks; the transport layer, handling host-to-host communication; and the application layer, providing process-to-process data exchange for applications.[27]
- Common link-layer protocols include Ethernet, Wi-Fi, and DSL.[28]
- The standard internet layer protocol is IP.[29]
- The standard transport layer protocols are TCP and UDP.[30]
- Common application layer protocols include:[31]
- HTTP and HTTPS (web)
- POP3, IMAP, and SMTP (email)
- FTP, FTPS, and SFTP (file transfer)
- SNMP (network monitoring)
- Packets are transmitted by switches and access points on local networks and by routers between networks.[32]
- The Domain Name System (DNS) is a hierarchical and decentralized naming system for computers, services, or other resources connected to the Internet or a private network. It associates various information with domain names assigned to each of the participating entities. Most prominently, it translates more readily memorized domain names to the numerical IP addresses needed for locating and identifying computer services and devices with the underlying network protocols.[33]
- A local area network (LAN) is a computer network that interconnects computers within a limited area such as a residence, school, laboratory, university campus or office building.[34]
- A wide area network (WAN) is a telecommunications network that extends over a large geographical area for the primary purpose of computer networking, often established with leased telecommunication circuits.[35]
Key Terms
[edit | edit source]- CSS (Cascading Style Sheets)
- A style sheet language used for describing the presentation of a document written in a markup language.[36]
- DSL (Digital Subscriber Line)
- A family of technologies that are used to transmit digital data over telephone lines.[37]
- FTP (File Transfer Protocol)
- A standard network protocol used for the transfer of computer files between a client and server on a computer network.[38]
- FTPS (File Transfer Protocol over Secure Sockets Layer)
- An extension to the commonly used File Transfer Protocol (FTP) that adds support for the Transport Layer Security (TLS) and the (now prohibited) Secure Sockets Layer (SSL) cryptographic protocols.[39]
- HTML (Hypertext Markup Language)
- The standard markup language for documents designed to be displayed in a web browser.[40]
- HTTP (Hypertext Transfer Protocol)
- An application protocol for distributed, collaborative, hypermedia information systems used as the foundation of data communication for the World Wide Web.[41]
- HTTPS (Hypertext Transfer Protocol Secure)
- An extension of the Hypertext Transfer Protocol (HTTP) used for secure communication encrypted using Transport Layer Security (TLS).[42]
- IMAP (Internet Mail Access Protocol)
- An Internet standard protocol used by e-mail clients to retrieve e-mail messages from a mail server.[43]
- IP (Internet Protocol)
- The principal communications protocol in the Internet protocol suite for relaying datagrams across network boundaries. Its routing function enables internetworking, and essentially establishes the Internet.[44]
- ISP (Internet Service Provider)
- An organization that provides services for accessing, using, or participating in the Internet.[45]
- POP (Post Office Protocol)
- An application-layer Internet standard protocol used by local e-mail clients to retrieve e-mail from a remote server over a TCP/IP connection.[46]
- POP3 (Post Office Protocol 3)
- The current version of the Post Office Protocol (POP).[47]
- SFTP (Secure File Transfer Protocol)
- A network protocol that provides file access, file transfer, and file management over any reliable data stream designed by the Internet Engineering Task Force (IETF) as an extension of the Secure Shell protocol (SSH) version 2.0 to provide secure file transfer capabilities.[48]
- SMTP (Simple Mail Transfer Protocol)
- An Internet standard for electronic mail (email) transmission.[49]
- SNMP (Simple Network Management Protocol)
- An Internet Standard protocol for collecting and organizing information about managed devices on IP networks and for modifying that information to change device behavior.[50]
- SSL (Secure Sockets Layer)
- An outdated encryption protocol replaced by Transport Layer Security (TLS).[51]
- TCP (Transmission Control Protocol)
- One of the main protocols of the Internet protocol suite, which provides reliable, ordered, and error-checked delivery of a stream of octets (bytes) between applications running on hosts communicating via an IP network.[52]
- TCP/IP (Transmission Control Protocol/Internet Protocol)
- Known as the Internet protocol suite, the conceptual model and set of communications protocols used in the Internet and similar computer networks.[53]
- URL (Uniform Resource Locator)
- A reference to a web resource that specifies its location on a computer network and a mechanism for retrieving it.[54]
- VoIP (Voice over Internet Protocol)
- A method and group of technologies for the delivery of voice communications and multimedia sessions over Internet Protocol (IP) networks, such as the Internet.[55]
Assessments
[edit | edit source]- Flashcards: Quizlet: IT Fundamentals - Internet
- Quiz: Quizlet: IT Fundamentals - Internet
See Also
[edit | edit source]References
[edit | edit source]- ↑ CompTIA: IT Fundamentals (ITF+) Exam Objectives FC0-U61
- ↑ Wikipedia: Internet service provider
- ↑ Wikipedia: Internet service provider
- ↑ Wikipedia: Internet service provider
- ↑ Wikipedia: Optical fiber
- ↑ Wikipedia: Cable Internet access
- ↑ Wikipedia: Digital subscriber line
- ↑ Wikipedia: Wireless
- ↑ Wikipedia: Wireless
- ↑ Wikipedia: Wi-Fi
- ↑ Wikipedia: Wi-Fi
- ↑ Wikipedia: Satellite Internet access
- ↑ Wikipedia: Mobile web
- ↑ Wikipedia: Web browser
- ↑ Wikipedia: Web browser
- ↑ Wikipedia: Web cache
- ↑ Wikipedia: Dynamic web page
- ↑ Wikipedia: Browser extension
- ↑ Wikipedia: Browser extension
- ↑ Wikipedia: Browser extension
- ↑ Wikipedia: Private browsing
- ↑ Wikipedia: Proxy server
- ↑ Wikipedia: Public key certificate
- ↑ Wikipedia: Pop-up ad
- ↑ Wikipedia: NoScript
- ↑ Wikipedia: Cross-browser compatibility
- ↑ Wikipedia: Internet protocol suite
- ↑ Wikipedia: Internet protocol suite
- ↑ Wikipedia: Internet protocol suite
- ↑ Wikipedia: Internet protocol suite
- ↑ Wikipedia: Internet protocol suite
- ↑ Wikipedia: Internet protocol suite
- ↑ Wikipedia: Domain Name System
- ↑ Wikipedia: Local area network
- ↑ Wikipedia: Wide area network
- ↑ Wikipedia: Cascading Style Sheets
- ↑ Wikipedia: Digital subscriber line
- ↑ Wikipedia: File Transfer Protocol
- ↑ Wikipedia: FTPS
- ↑ Wikipedia: HTML
- ↑ Wikipedia: Hypertext Transfer Protocol
- ↑ Wikipedia: HTTPS
- ↑ Wikipedia: Internet Message Access Protocol
- ↑ Wikipedia: Internet Protocol
- ↑ Wikipedia: Internet service provider
- ↑ Wikipedia: Post Office Protocol
- ↑ Wikipedia: Post Office Protocol
- ↑ Wikipedia: SSH File Transfer Protocol
- ↑ Wikipedia: Simple Mail Transfer Protocol
- ↑ Wikipedia: Simple Network Management Protocol
- ↑ Wikipedia: Transport Layer Security
- ↑ Wikipedia: Transmission Control Protocol
- ↑ Wikipedia: Internet protocol suite
- ↑ Wikipedia: URL
- ↑ Wikipedia: Voice over IP
Security Concepts
[edit | edit source]
This lesson introduces IT security concepts.
Objectives and Skills
[edit | edit source]Objectives and skills for the security concepts portion of IT Fundamentals certification include:[1]
- Compare and contrast authentication, authorization, accounting and non-repudiation concepts.
- Authentication
- Single factor
- Multifactor
- Examples of factors
- Password
- PIN
- One-time password
- Software token
- Hardware token
- Biometrics
- Specific location
- Security questions
- Single sign-on
- Authorization
- Permissions
- Least privilege model
- Role-based access
- User account types
- Rule-based access
- Mandatory access controls
- Discretionary access controls
- Accounting
- Logs
- Tracking
- Web browser history
- Non-repudiation
- Video
- Biometrics
- Signature
- Receipt
- Authentication
- Summarize confidentiality, integrity and availability concerns.
- Confidentiality concerns
- Snooping
- Eavesdropping
- Wiretapping
- Social engineering
- Dumpster diving
- Integrity concerns
- Man-in-the-middle
- Replay attack
- Impersonation
- Unauthorized information alteration
- Availability concerns
- Denial of service
- Power outage
- Hardware failure
- Destruction
- Service outage
- Confidentiality concerns
Readings
[edit | edit source]Multimedia
[edit | edit source]- YouTube: Authentication, Authorization, Accounting & Non-Repudiation
- YouTube: Confidentiality, Integrity & Availability Concerns
Activities
[edit | edit source]- Manage user accounts.
- Windows: Review GCF Global: Understanding user accounts. Create and test both administrator and standard accounts. Identify the differences between the two account types and when each one should be used.
- macOS: Review GCF Global: Understanding user accounts. Create and test both administrator and standard accounts. Identify the differences between the two account types and when each one should be used.
- Linux: Review Pluralsight: User and Group Management in Linux. Create and test both regular and super (sudoer) accounts. Identify the differences between the two account types and when each one should be used.
- Research multi-factor authentication. Consider setting up multi-factor authentication on all supported accounts, including Apple, Facebook, Google, and/or Microsoft accounts, as well as your password manager and your financial institutions.
- Manage permissions.
- Windows:
- Review Online Tech Tips: How to Set File and Folder Permissions in Windows.
- Check folder and file permissions for your Documents folder and one or more of the files in that folder.
- macOS:
- Review Apple: Change permissions for files, folders, or disks on Mac.
- Check folder and file permissions for your Documents folder and one or more of the files in that folder.
- Linux:
- Review Geeks for Geeks: Permissions in Linux
- Check folder and file permissions for your Documents folder and one or more of the files in that folder.
- Windows:
- Review security policy settings.
- Windows: Review Microsoft: Security policyConsider whether any security policy changes are necessary.
- macOS: Review Apple: Change Security & Privacy General preferences on Mac. Consider whether any security preference changes are necessary.
- Linux: Review Pluralsight: Linux Hardening - A 15-Step Checklist for a Secure Linux Server. Consider whether any security setting changes are necessary.
- Research confidentiality, integrity, and availability concerns for your school or work environment. What security risks exist? How can these risks be mitigated?
Lesson Summary
[edit | edit source]Authentication
[edit | edit source]- Authentication is the act of proving an assertion, such verifying the identity of a computer system user.[2]
- Multi-factor authentication is an authentication method in which a computer user is granted access only after successfully presenting two or more pieces of evidence (or factors) to an authentication mechanism:[3]
- knowledge (something the user and only the user knows)
- possession (something the user and only the user has)
- inherence (something the user and only the user is)
- Examples of factors include:[4]
- Password
- PIN
- One-time password
- Software token
- Hardware token
- Biometrics
- Specific location
- Security questions
- Single sign-on (SSO) is an authentication scheme that allows a user to log in with a single ID and password to any of several related, yet independent, software systems.[5]
Authorization
[edit | edit source]- Authorization is the function of specifying access rights/privileges to resources, which is related to information security and computer security in general and to access control in particular.[6]
- Permissions or access rights control the ability of users to view, change, navigate, and execute system resources.[7]
- The principle of least privilege (PoLP) requires that every module (such as a process, a user, or a program, depending on the subject) must be able to access only the information and resources that are necessary for its legitimate purpose.[8]
- Role-based access control (RBAC) or role-based security is an approach to restricting system access to authorized users based on job functions. The permissions to perform certain operations are assigned to specific roles. Members or staff (or other system users) are assigned particular roles, and through those role assignments acquire the permissions needed to perform particular system functions.[9]
- Common user account types may include guest, standard, power user, and administrator.[10]
- Rule-based access control extends role-based access by applying policies that express a complex Boolean rule set that can evaluate many different attributes. Attribute categories include:[11]
- Subject attributes: attributes that describe the user attempting the access e.g. age, clearance, department, role, job title
- Action attributes: attributes that describe the action being attempted e.g. read, delete, view, approve
- Object attributes: attributes that describe the object (or resource) being accessed e.g. the object type (medical record, bank account...), the department, the classification or sensitivity, the location
- Contextual (environment) attributes: attributes that deal with time, location or dynamic aspects of the access control scenario
- Mandatory access control (MAC) refers to a type of access control by which the operating system constrains the ability of a subject or initiator to access or generally perform some sort of operation on an object or target.[12]
- Discretionary access control (DAC) is a type of access control by which a subject with a certain access permission is capable of passing that permission (perhaps indirectly) on to any other subject (unless restrained by mandatory access control).[13]
Accounting
[edit | edit source]- Accounting within computer security refers to accountability, using such system components as audit trails (records) and logs, to associate a subject with its actions.[14]
- An audit trail (also called audit log) is a security-relevant chronological record, set of records, and/or destination and source of records that provide documentary evidence of the sequence of activities that have affected at any time a specific operation, procedure, or event.[15]
- Logs are files that record either events that occur in an operating system or other software runs.[16]
- Web browsing history is the list of web pages a user has visited recently, as well as associated data such as page title and time of visit, which is recorded by web browser software as standard for a certain period of time.[17]
Non-repudiation
[edit | edit source]- Non-repudiation involves associating actions or changes with a unique individual. This prevents the owner of the account from denying actions performed by the account.[18]
- Non-repudiation methods include:[19]
- Video
- Biometrics
- Digital Signature
- Receipt
Confidentiality
[edit | edit source]- Confidentiality involves a set of rules or a promise usually executed through agreements that limits access or places restrictions on certain types of information.[20]
- Snooping is stealthily observing any type of action or communication.[21][22]
- Eavesdropping is the act of secretly or stealthily listening to the private conversation or communications of others without their consent.[23]
- Wiretapping is the monitoring of telephone and Internet-based conversations by a third party, often by covert means.[24]
- Social engineering is the psychological manipulation of people into performing actions or divulging confidential information.[25]
- Dumpster diving is salvaging from garbage containers for items discarded by their owners, but deemed useful to the picker.[26]
Integrity
[edit | edit source]- Data integrity is the maintenance of, and the assurance of the accuracy and consistency of data over its entire life-cycle.[27]
- Man-in-the-middle attack is an attack where the attacker secretly relays and possibly alters the communications between two parties who believe that they are directly communicating with each other.[28]
- Replay attack is a form of network attack in which a valid data transmission is maliciously or fraudulently repeated or delayed. This is carried out either by the originator or by an adversary who intercepts the data and re-transmits it, possibly as part of a masquerade attack by IP packet substitution.[29]
- Impersonation is when someone imitates or copies the behavior or actions of another, often as part of a criminal act such as identity theft.[30]
- Unauthorized information alteration may occur with incomplete or incorrect implementation of authentication and authorization.[31]
Availability
[edit | edit source]- Availability is the degree to which a system, subsystem or equipment is in a specified operable and committable state at a given time.[32]
- A denial-of-service attack (DoS attack) is a cyber-attack in which the perpetrator seeks to make a machine or network resource unavailable to its intended users by temporarily or indefinitely disrupting services of a host connected to the Internet.[33]
- A power outage (also called a power cut, a power out, a power blackout, power failure or a blackout) is the loss of the electrical power network supply to an end user.[34]
- Computer security can be compromised by devices, such as keyboards, monitors or printers (thanks to electromagnetic or acoustic emanation for example) or by components of the computer, such as the memory, the network card or the processor (thanks to time or temperature analysis for example).[35]
- An asset is any data, device, or other component of the environment that supports information-related activities. Assets generally include hardware, software, and confidential information. Assets should be protected from illicit access, use, disclosure, alteration, destruction, and/or theft, resulting in loss to the organization.[36]
- Downtime refers to periods when a system is unavailable. Downtime or outage duration refers to a period of time that a system fails to provide or perform its primary function. Reliability, availability, recovery, and unavailability are related concepts.[37]
Key Terms
[edit | edit source]- ACL (Access Control List)
- A list of permissions attached to an object.[38]
- DDoS (Distributed Denial of Service)
- A distributed denial-of-service (DDoS) is a large-scale DoS attack where the perpetrator uses more than one unique IP address or machines, often from thousands of hosts infected with malware.[39]
- DLP (Data Leak Prevention)
- Preventing the intentional or unintentional release of secure or private/confidential information to an untrusted environment.[40]
- DoS (Denial of Service)
- A cyber-attack in which the perpetrator seeks to make a machine or network resource unavailable to its intended users by temporarily or indefinitely disrupting services of a host connected to the Internet.[41]
- IDS (Intrusion Detection System)
- A device or software application that monitors a network or systems for malicious activity or policy violations.[42]
- IPS (Intrusion Prevention System)
- Network security appliances that monitor network or system activities to identify malicious activity, log information about this activity, report it, and attempt to block or stop it.[43]
- MITM (Man in the Middle)
- An attack where the attacker secretly relays and possibly alters the communications between two parties who believe that they are directly communicating with each other.[44]
- ROSI (Return on Security Investment)
- A ratio between net benefit and cost of investment. As a performance measure, ROI is used to evaluate the efficiency of an investment or to compare the efficiencies of several different investments.[45]
- SID (System Identifier or Security Identifier)
- A unique, immutable identifier of a user, user group, or other security principal.[46]
Assessments
[edit | edit source]- Flashcards: Quizlet: IT Fundamentals - Security Concepts
- Quiz: Quizlet: IT Fundamentals - Security Concepts
See Also
[edit | edit source]References
[edit | edit source]- ↑ CompTIA: IT Fundamentals (ITF+) Exam Objectives FC0-U61
- ↑ Wikipedia: Authentication
- ↑ Wikipedia: Multi-factor authentication
- ↑ CompTIA: IT Fundamentals (ITF+) Exam Objectives FC0-U61
- ↑ Wikipedia: Single sign-on
- ↑ Wikipedia: Authorization
- ↑ Wikipedia: File system permissions
- ↑ Wikipedia: Principle of least privilege
- ↑ Wikipedia: Role-based access control
- ↑ Wikipedia: User (computing)
- ↑ Wikipedia: Attribute-based access control
- ↑ Wikipedia: Mandatory access control
- ↑ Wikipedia: Discretionary access control
- ↑ Wikipedia: Computer access control
- ↑ Wikipedia: Audit trail
- ↑ Wikipedia: Log file
- ↑ Wikipedia: Web browsing history
- ↑ Wikipedia: Non-repudiation
- ↑ CompTIA: IT Fundamentals (ITF+) Exam Objectives FC0-U61
- ↑ Wikipedia: Confidentiality
- ↑ Wikipedia: Snooping
- ↑ TechTarget: Snooping
- ↑ Wikipedia: Eavesdropping
- ↑ Wikipedia: Telephone tapping
- ↑ Wikipedia: Social engineering (security)
- ↑ Wikipedia: Dumpster diving
- ↑ Wikipedia: Data integrity
- ↑ Wikipedia: Man-in-the-middle attack
- ↑ Wikipedia: Replay attack
- ↑ Wikipedia: Impersonation
- ↑ Wikipedia: Computer access control
- ↑ Wikipedia: Availability
- ↑ Wikipedia: Denial-of-service attack
- ↑ Wikipedia: Power outage
- ↑ Wikipedia: Computer security compromised by hardware failure
- ↑ Wikipedia: Asset (computer security)
- ↑ Wikipedia: Downtime
- ↑ Wikipedia: Access control list
- ↑ Wikipedia: Denial-of-service attack
- ↑ Wikipedia: Data breach
- ↑ Wikipedia: Denial-of-service attack
- ↑ Wikipedia: Intrusion detection system
- ↑ Wikipedia: Intrusion detection system
- ↑ Wikipedia: Man-in-the-middle attack
- ↑ Wikipedia: Return on investment
- ↑ Wikipedia: Security Identifier
Security Practices
[edit | edit source]
This lesson introduces the best IT security practices.
Objectives and Skills
[edit | edit source]Objectives and skills for the security practices portion of IT Fundamentals certification include:[1]
- Explain methods to secure devices and best practices.
- Securing devices (mobile/workstation)
- Antivirus/Anti-malware
- Host firewall
- Changing default passwords
- Enabling passwords
- Safe browsing practices
- Patching/updates
- Device use best practices
- Software sources
- Validating legitimate sources
- Researching legitimate sources
- OEM websites vs. third-party websites
- Removal of unwanted software
- Removal of unnecessary software
- Removal of malicious software
- Software sources
- Securing devices (mobile/workstation)
- Explain password best practices.
- Password length
- Password complexity
- Password history
- Password expiration
- Password reuse across sites
- Password managers
- Password reset process
- Explain common uses of encryption.
- Plain text vs. cipher text
- Data at rest
- File level
- Disk level
- Mobile device
- Data in transit
- HTTPS
- VPN
- Mobile application
- Summarize behavioral security concepts.
- Expectations of privacy when using:
- The Internet
- Social networking sites
- File sharing
- Instant messaging
- Mobile applications
- Desktop software
- Business software
- Corporate network
- The Internet
- Written policies and procedures
- Handling of confidential information
- Passwords
- Personal information
- Customer information
- Company confidential information
- Expectations of privacy when using:
Readings
[edit | edit source]Multimedia
[edit | edit source]- YouTube: Devices Security Best Practices
- YouTube: Password Best Practices
- YouTube: Common Uses of Encryption
- YouTube: Behavioral Security Concepts
- YouTube: Chapter 11 - IT Fundamentals+ (FC0-U61) IT Security Threat Mitigation
Activities
[edit | edit source]- Complete the GCF Global: Protecting your computer tutorial.
- Use anti-malware software to scan your system and test malware detection.
- All: Review Wikipedia: Comparison of antivirus software. Download a free, well-known anti-malware application and scan your system.
- All: Review Wikipedia: EICAR test file. Download and save the EICAR test file to test your anti-malware application and follow the process for removing malware.
- Configure password management.
- All: Research password managers. Consider installing and using a password manager on your system.
- Windows: Review Microsoft: How to Configure Security Policy Settings. Consider modifying Password Policy and Account Lockout Policy settings.
- macOS: Review CNet: How to set up password policies in macOS. Consider modifying password restrictions.
- Linux: Review Xmodulo: How to set password policy on Linux. Consider modifying password policy settings.
- Test your firewall using a testing service such as Gibson Research: ShieldsUP!
- Consider encrypting your system storage:
- Windows: Review Microsoft: BitLocker Drive Encryption Overview
- macOS: Review Apple: macOS: About FileVault 2
- Linux: Review ArchLinux: Disk Encryption
- Android: Review GreenBot: Why and How to Encrypt Your Android Device.
- iOS: Review Apple:Understanding Data Protection.
- Research privacy options when using social networking, instant messaging, and various installed apps and programs. Consider enhancing your privacy settings wherever possible.
Lesson Summary
[edit | edit source]Device Security
[edit | edit source]- Device hardening is the process of securing a system by reducing its surface of vulnerability. Reducing available ways of attack typically includes changing default passwords, the removal of unnecessary software, unnecessary usernames or logins, and the disabling or removal of unnecessary services.[2]
- Antivirus software, also known as anti-malware, is a computer program used to prevent, detect, and remove malware.[3]
- A firewall is a network security system that monitors and controls incoming and outgoing network traffic based on predetermined security rules.[4]
- Firewalls are often categorized as either network firewalls or host-based firewalls. Network firewalls filter traffic between two or more networks and run on network hardware. Host-based firewalls run on host computers and control network traffic in and out of those machines.
- Securing devices includes:[5]
- Antivirus/Anti-malware
- Host firewall
- Changing default passwords
- Enabling passwords
- Safe browsing practices
- Patching/updates
- Best practices for device use include:[6]
- Software sources
- Validating legitimate sources
- Researching legitimate sources
- OEM websites vs. third-party websites
- Removal of unwanted software
- Removal of unnecessary software
- Removal of malicious software
- Software sources
Passwords
[edit | edit source]- A password is a memorized secret, typically a string of characters, used to confirm the identity of a user.[7]
- Password best practices include:[8]
- Password length
- Password complexity
- Password history (minimizing reuse)
- Password expiration
- Password reuse across sites (minimizing reuse)
- Password managers
- Password reset process
Encryption
[edit | edit source]- Encryption is the process of encoding information. This process converts the original representation of the information, known as plaintext, into an alternative form known as ciphertext.[9]
- Most applications of encryption protect information only at rest or in transit, leaving sensitive data in cleartext and potentially vulnerable to improper disclosure during processing.[10]
- File-level encryption is a form of disk encryption where individual files or directories are encrypted by the file system itself.[11]
- Disk-level encryption is a form of disk encryption where the entire partition or disk in which the file system resides is encrypted.[12]
- Email is encrypted using Transport Layer Security (TLS).[13]
- Web browser communication is encrypted using HTTPS.[14]
- A virtual private network (VPN) extends a private network across a public network and enables users to send and receive data across shared or public networks as if their computing devices were directly connected to the private network.[15]
Behavioral Security
[edit | edit source]- Internet privacy involves the right or mandate of personal privacy concerning the storing, repurposing, provision to third parties, and displaying of information pertaining to oneself via the Internet.[16]
- Those concerned about Internet privacy often cite a number of privacy risks — events that can compromise privacy — which may be encountered through online activities. These range from the gathering of statistics on users to more malicious acts such as the spreading of spyware and the exploitation of various forms of bugs (software faults).[17]
- A privacy policy is a statement or a legal document (in privacy law) that discloses some or all of the ways a party gathers, uses, discloses, and manages a customer or client's data.[18]
- Personal information can be anything that can be used to identify an individual, not limited to the person's name, address, date of birth, marital status, contact information, ID issue, and expiry date, financial records, credit information, medical history, where one travels, and intentions to acquire goods and services.[19]
Key Terms
[edit | edit source]- PII (Personally Identifiable Information)
- Any information relating to an identifiable person.[20]
- PIN (Personal Identification Number)
- A numeric or alpha-numeric password used in the process of authenticating a user accessing a system.[21]
- VPN (Virtual Private Network)
- Extends a private network across a public network and enables users to send and receive data across shared or public networks as if their computing devices were directly connected to the private network.[22]
Assessments
[edit | edit source]- Flashcards: Quizlet: IT Fundamentals - Security Practices
- Quiz: Quizlet: IT Fundamentals - Security Practices
See Also
[edit | edit source]References
[edit | edit source]- ↑ CompTIA: IT Fundamentals (ITF+) Exam Objectives FC0-U61
- ↑ Wikipedia: Hardening (computing)
- ↑ Wikipedia: Antivirus software
- ↑ Wikipedia: Firewall (computing)
- ↑ CompTIA: IT Fundamentals (ITF+) Exam Objectives FC0-U61
- ↑ CompTIA: IT Fundamentals (ITF+) Exam Objectives FC0-U61
- ↑ Wikipedia: Password
- ↑ CompTIA: IT Fundamentals (ITF+) Exam Objectives FC0-U61
- ↑ Wikipedia: Encryption
- ↑ Wikipedia: Encryption
- ↑ Wikipedia: File-level encryption
- ↑ Wikipedia: File-level encryption
- ↑ Wikipedia: Email encryption
- ↑ Wikipedia: HTTPS
- ↑ Wikipedia: Virtual private network
- ↑ Wikipedia: Internet privacy
- ↑ Wikipedia: Internet privacy
- ↑ Wikipedia: Privacy policy
- ↑ Wikipedia: Privacy policy
- ↑ Wikipedia: Personal data
- ↑ Wikipedia: Personal identification number
- ↑ Wikipedia: Virtual private network
Software Development
[edit | edit source]



This lesson introduces software development concepts.
Objectives and Skills
[edit | edit source]Objectives and skills for the software development portion of IT Fundamentals certification include:[1]
- Compare and contrast programming language categories.
- Interpreted
- Scripting languages
- Scripted languages
- Markup languages
- Compiled programming languages
- Query languages
- Assembly language
- Interpreted
- Explain the purpose and use of programming concepts.
- Identifiers
- Variables
- Constants
- Containers
- Arrays
- Vectors
- Functions
- Objects
- Properties
- Attributes
- Methods
- Identifiers
- Compare and contrast fundamental data types and their characteristics.
- Char
- Strings
- Numbers
- Integers
- Floats
- Boolean
- Given a scenario, use programming organizational techniques and interpret logic.
- Organizational techniques
- Pseudocode concepts
- Flow-chart concepts
- Sequence
- Logic components
- Branching
- Looping
- Organizational techniques
Readings
[edit | edit source]Multimedia
[edit | edit source]- YouTube: Programming Language Categories
- YouTube: Programming Concepts
- YouTube: Data Types
- YouTube: Programming Organizational Techniques & Interpreting Logic
- YouTube: Chapter 15 - IT Fundamentals+ (FC0-U61) Developing and Implementing Software
Activities
[edit | edit source]- Complete an interactive programming tutorial.
- Compare compiled and interpreted programming languages.
- C++
- Review Programming Fundamentals/Introduction/C++ and complete the activity using Repl.it.
- In the output window, run the
lscommand to list files in the current folder. Note themain.cppfile. - Run the program. Notice the two-step process of compiling main.cpp and then running main.
- In the output window, run the
lscommand to list files in the current folder. Note both themain.cppandmainfiles.
- Java
- Review Programming Fundamentals/Introduction/Java and complete the activity using Repl.it.
- In the output window, run the
lscommand to list files in the current folder. Note theMain.javafile. - Run the program. Notice the two-step process of compiling Main.java and then running Main.
- In the output window, run the
lscommand to list files in the current folder. Note both theMain.javaandMain.classfiles.
- Python
- Review Programming Fundamentals/Introduction/Python3 and complete the activity using Repl.it.
- In the output window, select
Help and shortcuts(question mark),Workspace shortcuts, and thenOpen shell. Run thelscommand to list files in the current folder. Note themain.pyfile. - Run the program. Notice the single-step process of running (interpreting) main.py.
- In the shell window, run the
lscommand to list files in the current folder. Note only themain.pyfile.
- C++
- Compare programming languages.
- Review Wikibooks: Computer Programming/Hello world. Compare source code examples for Assembly language, C++, HTML, Java, JavaScript, PowerShell, Python, SQL, and any other languages that interest you.
- Categorize each of these languages as compiled, interpreted, scripted, markup, query, or assembly language. Note the differences in coding style and intended purpose.
- Compare data types.
- Review Data Types and complete the activity using Repl.it.
- Note the characteristics for integer, floating-point, character, string, and Boolean values.
- Consider different uses for each variable type. Provide examples for when you could and could not use each type.
- Research and compare each of the following programming concepts.
- variables and constants
- arrays and vectors
- functions and subroutines
- Research object-oriented programming.
- Review Object-Oriented Programming/Introduction.
- Note the differences between objects, classes, properties, attributes, and methods.
Lesson Summary
[edit | edit source]Programming Language Categories
[edit | edit source]- A programming language is a formal language which comprises a set of instructions that produce various kinds of output.[2]
- An implementation of a programming language provides a way to write programs in that language and execute them on one or more configurations of hardware and software. There are, broadly, two approaches to programming language implementation: compilation and interpretation.[3]
- A compiled language is a programming language whose implementations are typically compilers (translators that generate machine code from source code). Compiled languages include C++ and Java.[4]
- An interpreted language is a type of programming language for which most of its implementations execute instructions directly and freely, without previously compiling a program into machine-language instructions. Interpreted languages include JavaScript, Perl, and Python.[5]
- Programs that are executed directly on the hardware usually run much faster than those that are interpreted in software.[6]
- A scripting or script language is a programming language for a special run-time environment that automates the execution of tasks. The tasks could alternatively be executed one-by-one by a human operator. Scripting languages are often interpreted (rather than compiled). Scripting languages include Perl, PowerShell, and Python.[7]
- A markup language is a system for annotating a document in a way that is syntactically distinguishable from the text, meaning when the document is processed for display, the markup language is not shown, and is only used to format the text. Markup languages include HTML.[8]
- Query languages are used to make queries in databases and information systems. Query languages include SQL.[9]
- Assembly language is any low-level programming language in which there is a very strong correspondence between the instructions in the language and the architecture's machine code instructions. Each assembly language is specific to a particular computer architecture and sometimes to an operating system.[10]
Programming Concepts
[edit | edit source]- Identifiers are tokens or symbols which name language entities. Some of the kinds of entities an identifier might denote include variables, constants, types, labels, subroutines, and packages.[11]
- A variable is a storage address (identified by a memory address) paired with an associated symbolic name, which contains some known or unknown quantity of information referred to as a value. In imperative programming languages, values can generally be accessed or changed at any time.[12]
- A constant is a value that cannot be altered by the program during normal execution. When associated with an identifier, a constant is said to be "named," although the terms "constant" and "named constant" are often used interchangeably.[13]
- A container is a data type whose instances are collections of other objects. Examples include arrays and vectors.[14]
- An array is a data structure consisting of a collection of elements (values or variables), each identified by at least one array index or key.[15]
- A vector is an array of object references. For example a multidimensional array may be implemented as an array of arrays.[16]
- A subroutine is a sequence of program instructions that performs a specific task, packaged as a unit. This unit can then be used in programs wherever that particular task should be performed. In different programming languages, a subroutine may be called a procedure, a function, a routine, a method, or a subprogram.[17]
- Some programming languages distinguish between functions or function subprograms, which provide an explicit return value to the calling program, and subroutines or procedures, which do not.[18]
- In object-oriented programming, object refers to a particular instance of a class, where the object can be a combination of variables, functions, and data structures.[19]
- An attribute defines a property of an object. For example, an object might have a color attribute.[20]
- A method is a procedure or function associated with an object. It is something the object does, such as move.[21]
- A property is a special sort of class member, intermediate in functionality between an attribute and a method. It provides a callable interface to access an attribute, allowing a property to perform data validation for the attribute or be read-only.[22]
Data Types
[edit | edit source]A data type is an attribute of data which tells the compiler or interpreter how the programmer intends to use the data.[23]
- A char is a character. Examples of characters include letters, numerical digits, common punctuation marks, and whitespace.[24]
- A string is a sequences of characters, either as a literal constant or as some kind of variable. Examples include "Hello" and "world!" Note that "12345" with quotes is a string rather than a numeric value.[25]
- An integer represents some range of mathematical whole numbers, values that may be represented without a fractional component. Examples include 1, 234, -5, and 0.[26][27]
- A float represents some range of mathematical real numbers, expressed with decimal points and a limited number of significant digits. Examples include 1.23, 3.14159, -2.71828 and 0.0[28]
- Most programming languages support floats with either seven significant digits (four bytes) or 15 significant digits (eight bytes). Eight-byte floating-point values are often referred to as double precision, or just double.[29]
- A Boolean represents one of two possible values (usually denoted true and false) which is intended to represent the two truth values of logic and Boolean algebra. The actual stored values are typically either 0 and 1 (false, true) or 0 and -1 (false, true), depending on the given programming language.[30]
Program Structure
[edit | edit source]- Structured programming is a programming paradigm aimed at improving the clarity, quality, and development time of a computer program by making extensive use of the structured control flow constructs of selection (if/then/else) and repetition (while and for), block structures, and subroutines.[31]
- Pseudocode (false or fake code) is an informal high-level description of the operating principle of a computer program or other algorithm. It uses the structural conventions of a normal programming language, but is intended for human reading rather than machine reading.[32]
- A flowchart is a type of diagram that represents a workflow or process. A flowchart can also be defined as a diagrammatic representation of an algorithm, a step-by-step approach to solving a task.[33]
- In structured programming, the ordered sequencing of successive commands is considered one of the basic control structures, alongside iteration, recursion and choice.[34]
- Logical comparisons are made using logical operators:[35][36]
- equal (==)
- less than (<)
- greater than (>)
- less than or equal (<=)
- greater than or equal (>=)
- not equal (!=)
- and (&&)
- or (||)
- not (!)
- A branch is an instruction in a computer program that can cause a computer to begin executing a different instruction sequence and thus deviate from its default behavior of executing instructions in order. Branch instructions are used to implement control flow in program loops and conditionals (i.e., executing a particular sequence of instructions only if certain conditions are satisfied).[37]
- A loop is a sequence of statements which is specified once but which may be carried out several times in succession. The code "inside" the loop (the body of the loop) is obeyed a specified number of times, or once for each of a collection of items, or until some condition is met, or indefinitely.[38]
Tips
[edit | edit source]- Data portability
- Make sure the end user is able to export and back up their user data, especially if stored in a closed environment.
Key Terms
[edit | edit source]- DLL (Dynamic Link Layer)
- Microsoft's implementation of the shared library concept in the Microsoft Windows operating system.[39]
- TLS (Thread Local Storage)
- A computer programming method that uses static or global memory local to a thread.[40]
Assessments
[edit | edit source]- Flashcards: Quizlet: IT Fundamentals - Software Development
- Quiz: Quizlet: IT Fundamentals - Software Development
See Also
[edit | edit source]References
[edit | edit source]- ↑ CompTIA: IT Fundamentals (ITF+) Exam Objectives FC0-U61
- ↑ Wikipedia: Programming language
- ↑ Wikipedia: Programming language
- ↑ Wikipedia: Compiled language
- ↑ Wikipedia: Interpreted language
- ↑ Wikipedia: Programming language
- ↑ Wikipedia: Scripting language
- ↑ Wikipedia: Markup language
- ↑ Wikipedia: Query language
- ↑ Wikipedia: Assembly language
- ↑ Wikipedia: Identifier (computer languages)
- ↑ Wikipedia: Variable (computer science)
- ↑ Wikipedia: Constant (computer programming)
- ↑ Wikipedia: Container (abstract data type)
- ↑ Wikipedia: Array data structure
- ↑ Wikipedia: Array data structure
- ↑ Wikipedia: Subroutine
- ↑ Wikipedia: Subroutine
- ↑ Wikipedia: Object (computer science)
- ↑ Wikipedia: Attribute (computing)
- ↑ Wikipedia: Method (computer programming)
- ↑ Wikipedia: Property (programming)
- ↑ Wikipedia: Data type
- ↑ Wikipedia: Character (computing)
- ↑ Wikipedia: String (computer science)
- ↑ Wikipedia: Integer (computer science)
- ↑ Wikipedia: Integer
- ↑ Wikipedia: Floating point
- ↑ Wikipedia: Floating point
- ↑ Wikipedia: Boolean data type
- ↑ Wikipedia: Structured programming
- ↑ Wikipedia: Pseudocode
- ↑ Wikipedia: Flowchart
- ↑ Wikipedia: Control flow
- ↑ Wikipedia: Relational operator
- ↑ Wikipedia: Logical operation
- ↑ Wikipedia: Branch (computer science)
- ↑ Wikipedia: Control flow
- ↑ Wikipedia: Dynamic-link library
- ↑ Wikipedia: Thread-local storage
Troubleshooting
[edit | edit source]
This lesson introduces IT troubleshooting methodology.
Objectives and Skills
[edit | edit source]Objectives and skills for the troubleshooting portion of IT Fundamentals certification include:[1]
- Explain the troubleshooting methodology.
- Identify the problem
- Gather information
- Duplicate the problem, if possible
- Question users
- Identify symptoms
- Determine if anything has changed
- Approach multiple problems individually
- Research knowledge base/ Internet, if applicable
- Establish a theory of probable cause
- Question the obvious
- Consider multiple approaches
- Divide and conquer
- Test the theory to determine the cause
- Once the theory is confirmed (confirmed root cause), determine the next steps to resolve the problem
- If the theory is not confirmed, establish a new theory or escalate
- Establish a plan of action to resolve the problem and identify potential effects
- Implement the solution or escalate as necessary
- Verify full system functionality and, if applicable, implement preventive measures
- Document findings/lessons learned, actions, and outcomes
- Identify the problem
Readings
[edit | edit source]Multimedia
[edit | edit source]- YouTube: Troubleshooting Methodology
- YouTube: Chapter 13 - IT Fundamentals+ (FC0-U61) IT Troubleshooting
Activities
[edit | edit source]- Select a recent or frequent technology problem you have had at school, work, or home. Explain how you would solve the problem following the troubleshooting methodology. Include the problem description and symptoms, resources searched, theories tested, problem resolution, and how you would document the issue and prevent it from recurring.
- Test Internet connectivity:
- Verify a physical connection:
- Wired: Check for connectivity lights on the network adapter and switch or router.
- Wireless: Check for connectivity through the user interface.
- Verify ip address settings.
- Windows: Use
ipconfig. - macOS: Use Network Utility, System Preferences / Network, or
ifconfig. - Linux: Use Network Configuration, System Settings / Networking, or
ifconfig.
- Windows: Use
- Review Ping/Host. Verify local and remote connectivity using
ping.- Ping your local IP address.
- Ping your local default gateway address.
- Ping an Internet host such as 8.8.8.8.
- Review Nslookup. Verify name resolution using
nslookupand an Internet host name, such as en.wikiversity.org.
- Verify a physical connection:
- View system recovery options.
- All: Review Wikipedia: Single-user mode.
- Windows: Boot into Safe Mode and/or the Recovery Console. View available options but do not make any changes. Restart the system normally when you are finished.
- macOS: Boot into single-user mode. View available options but do not make any changes. Restart the system normally when you are finished.
- Linux: Boot into single-user mode. View available options but do not make any changes. Restart the system normally when you are finished.
Lesson Summary
[edit | edit source]Troubleshooting
[edit | edit source]- Troubleshooting is a form of problem solving, often applied to repair failed products or processes on a machine or a system. It is a logical, systematic search for the source of a problem in order to solve it, and make the product or process operational again. Troubleshooting is needed to identify the symptoms. Determining the most likely cause is a process of elimination—eliminating potential causes of a problem. Finally, troubleshooting requires confirmation that the solution restores the product or process to its working state.[2]
Troubleshooting Methodology
[edit | edit source]- Troubleshooting methodology includes:[3]
- Identify the problem
- Gather information
- Duplicate the problem, if possible
- Question users
- Identify symptoms
- Determine if anything has changed
- Approach multiple problems individually
- Research knowledge base/ Internet, if applicable
- Establish a theory of probable cause
- Question the obvious
- Consider multiple approaches
- Divide and conquer
- Test the theory to determine the cause
- Once the theory is confirmed (confirmed root cause), determine the next steps to resolve the problem
- If the theory is not confirmed, establish a new theory or escalate
- Establish a plan of action to resolve the problem and identify potential effects
- Implement the solution or escalate as necessary
- Verify full system functionality and, if applicable, implement preventive measures
- Document findings/lessons learned, actions, and outcomes
Key Terms
[edit | edit source]- EMI (Electromagnetic Interference)
- A disturbance generated by an external source that affects an electrical circuit by electromagnetic induction, electrostatic coupling, or conduction.[4]
- ESD (Electrostatic Discharge)
- The sudden flow of electricity between two electrically charged objects caused by contact, an electrical short, or dielectric breakdown.[5]
- safe mode
- A diagnostic mode of a computer operating system. In Windows, safe mode only allows essential system programs and services to start up at boot. It is widely used for removing rogue security software.[6]
- single user mode
- A mode in which a multiuser computer operating system boots into a single superuser, common on Unix-like systems including macOS and Linux.[7]
Assessments
[edit | edit source]- Flashcards: Quizlet: IT Fundamentals - Troubleshooting
- Quiz: Quizlet: IT Fundamentals - Troubleshooting
See Also
[edit | edit source]References
[edit | edit source]Business Continuity
[edit | edit source]



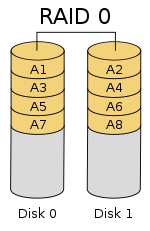




This lesson introduces business continuity through IT fault tolerance and disaster recovery.
Objectives and Skills
[edit | edit source]Objectives and skills for the business continuity portion of IT Fundamentals certification include:[1]
- Explain business continuity concepts.
- Fault tolerance
- Replication
- Redundancy
- Data
- Network
- Power
- Backup considerations
- Data
- File backups
- Critical data
- Database
- OS backups
- Location
- Stored locally
- Cloud storage
- On-site vs. off-site
- Contingency plan
- Disaster recovery
- Data restoration
- Prioritization
- Restoring access
- Fault tolerance
Readings
[edit | edit source]Multimedia
[edit | edit source]Activities
[edit | edit source]- Research cloud-based backup storage providers for your home or work environment. What service would you use? How much would it cost? If you don't already have an off-site backup solution, create one now.
- Research redundant Internet service providers for your home or work environment. What service would you use (wired, wireless, etc.)? How much would it cost? Would this be a good investment?
- Consider disaster recovery options for your home or work environment. If you were to lose access to all existing technology resources, how would you restore service? Describe how you would restore data and Internet access and how you would prioritize service restoration. Would you recommend maintaining a hot, warm, cold, or standby solution? Why?
Lesson Summary
[edit | edit source]Fault Tolerance
[edit | edit source]- Fault tolerance is the property that enables a system to continue operating properly in the event of the failure of (or one or more faults within) some of its components.[2]
- Replication provides multiple identical instances of the same system or subsystem, directing tasks or requests to all of them in parallel, and choosing the correct result on the basis of a quorum.[3]
- Redundancy provides multiple identical instances of the same system and switching to one of the remaining instances in case of a failure (failover).[4]
- Redundant resource needs include:[5]
- Data
- Network
- Power
- A backup is a copy of computer data taken and stored elsewhere so that it may be used to restore the original after a data loss event.[6]
- Backup options include full, incremental, differential, and copy.[7]
- A full backup contains a complete copy of the source taken at a specific point in time.[8]
- An incremental backup stores data changed since a reference point in time.[9]
- A differential backup saves only the data that has changed since the last full backup.[10]
- Some filesystems have an archive bit for each file that says it was recently changed. Some backup software looks at the date of the file and compares it with the last backup to determine whether the file was changed.[11]
- Full and incremental backups clear the archive bit. Differential and copy backups do not change the archive bit.[12]
- Backup considerations include:[13]
- Data
- File backups
- Critical data
- Database
- OS backups
- Location
- Stored locally
- Cloud storage
- On-site vs. off-site
- A contingency plan is a plan devised for an outcome other than in the usual (expected) plan. It is often used for risk management for an exceptional risk that, though unlikely, would have catastrophic consequences.[14]
Disaster Recovery
[edit | edit source]- Disaster Recovery involves a set of policies, tools and procedures to enable the recovery or continuation of vital technology infrastructure and systems following a natural or human-induced disaster.[15]
- Disaster recovery considerations include:[16]
- Data restoration
- Prioritization
- Restoring access
Key Terms
[edit | edit source]- RAID ("Redundant Array of Inexpensive Disks" or "Redundant Array of Independent Disks")
- A data storage virtualization technology that combines multiple physical disk drive components into one or more logical units for the purposes of data redundancy, performance improvement, or both.[17]
- RAID 0
- Consists of striping, but no mirroring or parity.[18]
- RAID 1
- Consists of data mirroring, without parity or striping.[19]
- RAID 5
- Consists of block-level striping with distributed parity.[20]
- RAID 10
- Consists of a striped set of mirrored drives.[21]
- UPS (uninterruptible power supply)
- An electrical apparatus that provides emergency power to a load when the input power source or mains power fails.[22]
Assessments
[edit | edit source]- Flashcards: Quizlet: IT Fundamentals - Business Continuity
- Quiz: Quizlet: IT Fundamentals - Business Continuity
See Also
[edit | edit source]References
[edit | edit source]- ↑ CompTIA: IT Fundamentals (ITF+) Exam Objectives FC0-U61
- ↑ Wikipedia: Fault tolerance
- ↑ Wikipedia: Fault tolerance
- ↑ Wikipedia: Fault tolerance
- ↑ CompTIA: IT Fundamentals (ITF+) Exam Objectives FC0-U61
- ↑ Wikipedia: Backup
- ↑ Wikipedia: Backup
- ↑ Wikipedia: Backup
- ↑ Wikipedia: Backup
- ↑ Wikipedia: Backup
- ↑ Wikipedia: Backup
- ↑ Wikipedia: Backup
- ↑ CompTIA: IT Fundamentals (ITF+) Exam Objectives FC0-U61
- ↑ Wikipedia: Contingency plan
- ↑ Wikipedia: Disaster recovery
- ↑ CompTIA: IT Fundamentals (ITF+) Exam Objectives FC0-U61
- ↑ Wikipedia: RAID
- ↑ Wikipedia: RAID
- ↑ Wikipedia: RAID
- ↑ Wikipedia: RAID
- ↑ Wikipedia: RAID
- ↑ Wikipedia: Uninterruptible power supply
